Seems to be will be deceiving, a lot in order that the acquainted icon might masks malware designed to steal your knowledge and cash.
06 Oct 2025
•
,
5 min. learn
PDF recordsdata have change into a staple of our day by day digital lives, each at work and at house. They work seamlessly throughout working methods and gadgets, they usually couldn’t be simpler to create and share. Day-after-day, numerous PDF (Moveable Doc Format) recordsdata are exchanged throughout inboxes and messaging platforms, and chances are high, you’ve opened one right now and not using a second thought.
Nevertheless, this all can also be partly what makes PDFs the proper disguise for all method of threats. At first look, PDF recordsdata appear about as benign as digital recordsdata get. To the bare eye, a malware-laced PDF or, certainly, one other file kind spreading underneath the guise of a PDF doesn’t essentially look a lot completely different from an abnormal bill, resume or authorities kind.
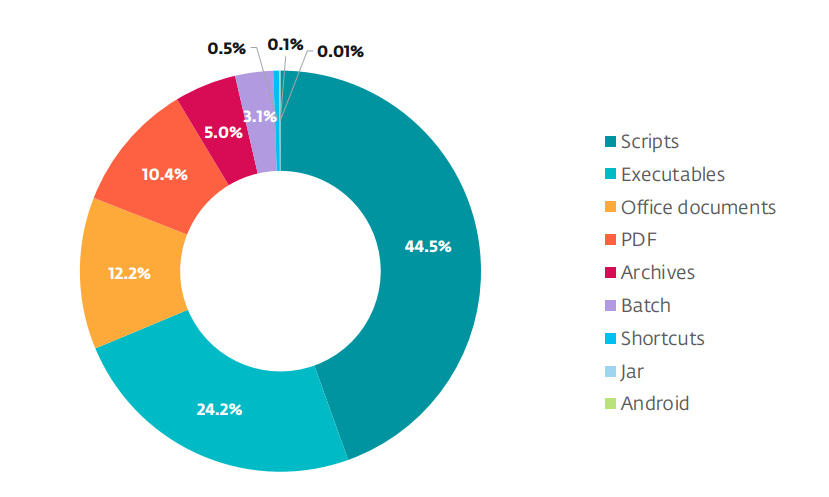
Safety researchers are seeing PDF recordsdata present up repeatedly as lures particularly in mass social engineering campaigns, but in addition in APT group operations and even in refined zero-day assaults. Latest ESET telemetry confirms that PDFs rank among the many prime file varieties abused in malicious campaigns.
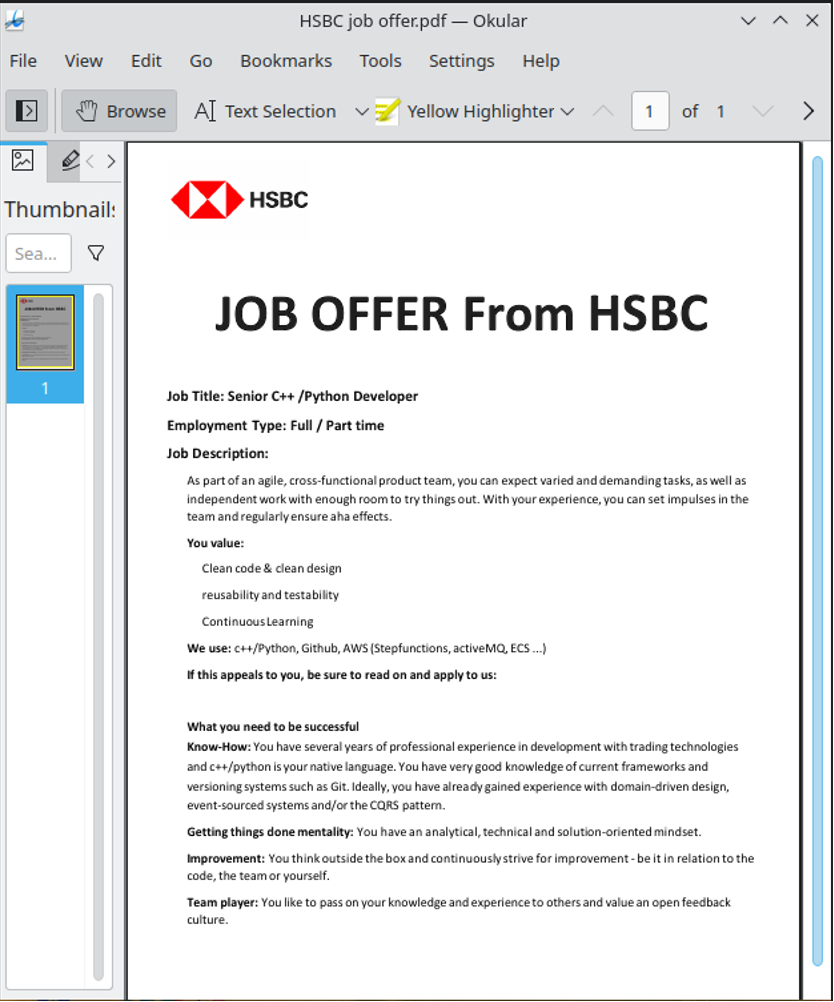
A wolf in sheep’s clothes
Booby-trapped PDFs usually arrive as e mail attachments or hyperlinks in phishing messages that trick victims into taking motion. As is frequent with social engineering campaigns, the lures are fastidiously crafted to spark emotion, corresponding to urgency (assume “last discover”), concern (“account suspended”) or curiosity (“take a look at outcomes accessible”). The top objective is to get you to decrease your guard and utilizing all method of exhortations, corresponding to “pay now” and “overview instantly”, strain you into opening a file or clicking a hyperlink.
The assault strategies range and have through the years included:
- Embedded scripts that run when the file opens, letting attackers launch numerous actions and deploy extra payloads. JavaScript in PDFs can carry out reliable duties, corresponding to creating interactive kinds and automating processes, nevertheless it’s additionally abused to obtain or execute code.
- Hidden or malicious hyperlinks: Hyperlinks contained within the PDF can redirect you to credential-harvesting pages or immediate you to obtain a malicious ZIP archive or executable.
- Exploiting vulnerabilities in PDF readers: Malformed objects or specifically crafted content material can benefit from bugs in weak variations of frequent PDF readers and result in code execution, as was the case with a software program loophole affecting Adobe Reader and documented by ESET researchers.
- Recordsdata that solely pose as PDFs and are as a substitute scripts, executables and even malicious Microsoft Workplace recordsdata, amongst others, however their true file extensions could also be hidden. Whereas you may even see a file known as “bill.pdf”, clicking it really launches an executable.
Talking of which, earlier this 12 months we wrote a couple of marketing campaign that distributed the Grandoreiro banking trojan and began with an e mail urging the sufferer to open a doc, ostensibly in PDF format. In actuality, it’s a ZIP archive containing, amongst different issues, a VBScript file that unleashes Grandoreiro on the system and finally provides criminals entry to the sufferer’s banking credentials.


Easy methods to spot a suspicious PDF
So what are the crimson flags that ought to put you on excessive alert?
- The file has a deceptive seen title or double extension. That is the case with names like bill.pdf.exe or doc.pdf.scr, particularly the place attackers solid their nets extensive and intend to ensnare as many individuals as potential. These recordsdata really aren’t PDFs in any respect – they’re simply dressed as much as appear to be PDFs.
- The sender’s e mail deal with or title doesn’t match what the file says. The e-mail sender’s deal with is completely different from the group that the doc claims to be from, or the area is misspelled or suspicious.
- The PDF is compressed inside a ZIP or RAR archive. The PDF arrives inside a ZIP or RAR – that’s in a bid to bypass detection by e mail filters.
- Your complete message is surprising or sounds “out of context”. Ask your self: did I ask for this file? Do I do know the sender? Does it make sense for them to ship it to me?
What to do if you happen to obtain a suspicious PDF
If a PDF raises crimson flags, take these precautions:
- Resist the temptation to right away obtain or open the file. The adage “when unsure, kick it out” works right here properly.
- Confirm the sender and context. Earlier than opening the doubtless sketchy attachment, contact the sender by a separate communication channel, corresponding to a telephone name, to verify that they’ve actually despatched it.
- Examine the file extension and dimension. Toggle “present file extensions” or related in your working system and make sure the file is an actual .pdf (not an .exe, for instance) and that the file dimension appears believable.
- Scan the file together with your safety software program (or alternatively, add it to VirusTotal to get a fast first look).
- Open with care. If you happen to completely should open it and have taken the opposite precautions, use an up-to-date PDF viewer with sandboxing or a protected view function enabled (corresponding to Adobe’s Protected View).
What to do if you happen to suspect you’ve opened a sketchy PDF
- Disconnect from the web to cut back the possibility of knowledge exfiltration or additional payload downloads.
- Run a full laptop scan with an up to date safety resolution. If you happen to don’t have any, run a one-time verify as accessible courtesy of ESET’s free scanner.
- Examine operating processes and community connections for anomalies. If you happen to’re not skilled, get an expert to research.
- Change passwords particularly to your monetary and different precious accounts, significantly the place you think your credentials might have been stolen – however achieve this from a tool apart from the one the place you downloaded the PDF.
- Report the incident to your IT/safety staff (in case you opened the file in your work machine).
Parting ideas
These tried-and-tested guidelines will go a great distance in direction of protecting you protected from dodgy PDFs:
- If you happen to weren’t anticipating the file, don’t open it, no less than not with out checking first that the file is reliable.
- Educate your self on how one can acknowledge phishing scams.
- As many assaults depend on identified software program vulnerabilities, maintain your working system and all different software program, together with PDF readers, up-to-date.
- Allow Protected View or sandbox mode in your PDF reader of alternative and contemplate adjusting or disabling your JavaScript settings in it.
- Use respected, multi-layered safety software program on all of your gadgets.
It’s protected to say that cybercriminals will proceed to use the belief we place in PDFs. The usage of PDFs for malicious ends can also be a reminder that safety threats usually don’t arrive wrapped in suspicious-looking recordsdata. The tried-and-true rule applies right here, too: Deal with each surprising hyperlink and attachment with warning and depend on trusted instruments to guard your knowledge and gadgets.











