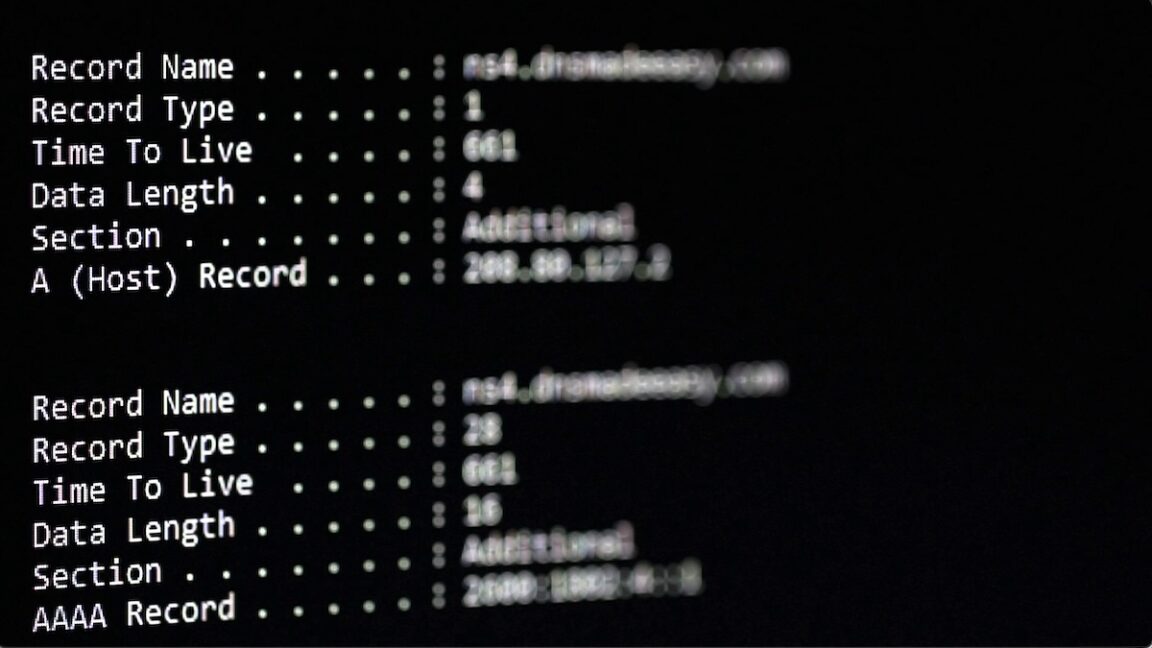
Hackers are stashing malware in a spot that’s largely out of the attain of most defenses—inside area title system (DNS) information that map domains to their corresponding numerical IP addresses.
The observe permits malicious scripts and early-stage malware to fetch binary information with out having to obtain them from suspicious websites or connect them to emails, the place they continuously get quarantined by antivirus software program. That’s as a result of site visitors for DNS lookups typically goes largely unmonitored by many safety instruments. Whereas internet and e mail site visitors is commonly carefully scrutinized, DNS site visitors largely represents a blind spot for such defenses.
An odd and enchanting place
Researchers from DomainTools on Tuesday stated they not too long ago noticed the trick getting used to host a malicious binary for Joke Screenmate, a pressure of nuisance malware that interferes with regular and secure features of a pc. The file was transformed from binary format into hexadecimal, an encoding scheme that makes use of the digits 0 by 9 and the letters A by F to symbolize binary values in a compact mixture of characters.
The hexadecimal illustration was then damaged up into a whole lot of chunks. Every chunk was stashed contained in the DNS report of a unique subdomain of the area whitetreecollective[.]com. Particularly, the chunks had been positioned contained in the TXT report, a portion of a DNS report able to storing any arbitrary textual content. TXT information are sometimes used to show possession of a web site when organising providers like Google Workspace.
An attacker who managed to get a toehold right into a protected community might then retrieve every chunk utilizing an innocuous-looking sequence of DNS requests, reassembling them, after which changing them again into binary format. The method permits the malware to be retrieved by site visitors that may be arduous to carefully monitor. As encrypted types of IP lookups—referred to as DOH (DNS over HTTPS) and DOT (DNS over TLS)—acquire adoption, the issue will seemingly develop.


![Why Each Staff Wants a Content material Engineer [MozCon 2025 Speaker Series]](https://blog.aimactgrow.com/wp-content/uploads/2025/09/MozCon-25-Speaker-Profile-Cards-15-120x86.png)