Verify your system for Axios npm Bundle variations 1.14.1 and 0.30.4 and take away them instantly to stop information theft.
Trendy net improvement depends closely on shared libraries, and few are as essential as Axios, a instrument that manages how purposes speak to servers. On 31 March 2026, this belief was damaged when a provide chain assault ‘poisoned’ the library. With Axios utilized in roughly 80% of cloud environments and seeing 100 million (101,032,032) weekly downloads, this is among the most impactful npm compromises on document.
A Speedy-Fireplace Account Takeover
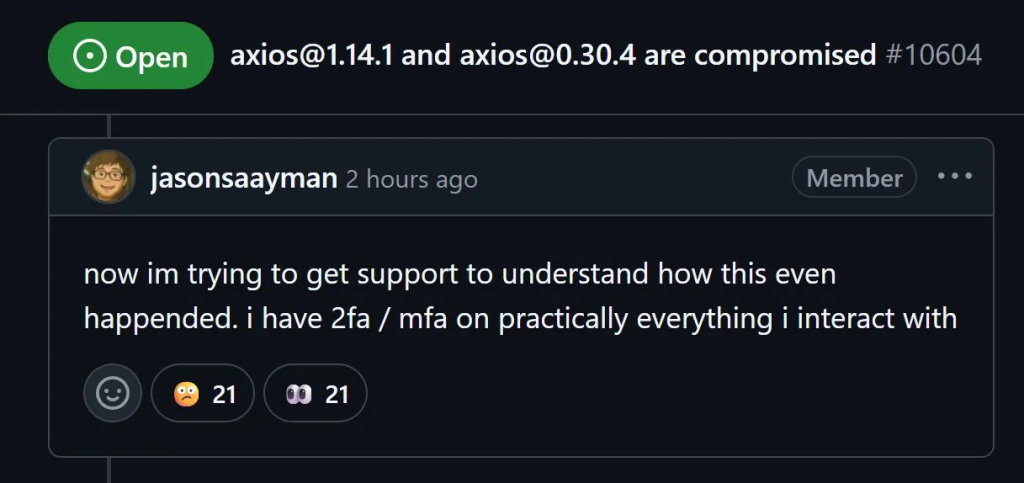
The breach started when a menace actor hijacked the GitHub and npm accounts of lead maintainer Jason Saayman. In keeping with analysis by Socket and OpenSourceMalware, this allowed the attacker to bypass commonplace safety checks like OIDC signing, which normally confirm code as trusted.
By 00:21 UTC, the hacker printed [email protected], adopted by [email protected]. Each have been pushed straight through a command-line interface slightly than the official automated pipeline. The primary an infection was recorded simply 89 seconds later. Whereas collaborators like DigitalBrainJS rushed to alert the neighborhood, the attacker used stolen admin privileges to delete GitHub points reporting the hack, taking part in a high-stakes cat-and-mouse recreation with safety groups for over three hours.
In keeping with weblog posts from Socket and OpenSourceMalware researchers, the precise payload was hidden inside a pretend dependency referred to as plain-crypto-js. Staged 24 hours prior, this Computer virus was designed to appear to be an ordinary encryption library. As soon as a developer put in the poisoned Axios, a script inside plain-crypto-js instantly went to work.
A separate analysis from Huntress reveals the malware’s superior stealth. As a multi-platform Distant Entry Trojan (RAT), it tailored to its atmosphere: on Home windows, it renamed itself wt.exe to imitate Home windows Terminal; on Macs, it hid as com.apple.act.mond to appear to be a local system course of. As soon as lively, the malware carried out a self-destruct sequence, deleting its personal recordsdata to take away any proof of the an infection.
Spying and Knowledge Theft
The results for contaminated machines are extreme. The malware established a connection to a command-and-control server at sfrclak.com:8000, sending a heartbeat sign each 60 seconds. This beacon included a ‘fingerprint’ of the sufferer’s machine, together with lively processes and listing dumps of delicate folders like .ssh, Paperwork, and OneDrive.
The attackers weren’t simply in search of recordsdata; they have been in search of a foothold. The RAT allowed them to remotely execute instructions, inject new binaries, or seize cloud API tokens. This successfully gave hackers a remote-control window into any developer’s machine that ran an ordinary npm set up through the three-hour compromise window.
What to Do If You’re Affected
When you carried out a construct or replace between 00:21 and 03:40 UTC on 31 March, your system is probably going in danger. Verify your lockfiles for Axios variations 1.14.1 or 0.30.4 and the plain-crypto-js bundle.
As a result of the malware survives reboots and hides from fundamental antivirus, specialists from all three companies suggest a ‘scorched earth’ strategy. Don’t try to patch the system; as a substitute, wipe the machine fully, reinstall the OS, and instantly rotate each secret, key, and password saved on that system.