There’s an app for the whole lot these days… proper? Effectively, wanting up name data for a cellphone variety of selection is not a type of issues, as doubtlessly thousands and thousands of Android customers came upon after paying for app subscriptions promising simply that.
The offending apps, which we named CallPhantom based mostly on their false claims, purport to offer entry to name histories, SMS data, and even WhatsApp name logs for any cellphone quantity. To unlock this supposed function, customers are requested to pay – however all they get in return is randomly generated knowledge.
Our investigation recognized 28 such fraudulent apps accessible on the Google Play retailer, cumulatively downloaded greater than 7.3 million occasions. As an App Protection Alliance accomplice, we reported our findings to Google, which eliminated all the apps recognized on this report from Google Play.
Key factors of this blogpost:
- A brand new Android rip-off, CallPhantom, falsely claims to offer entry to name logs, SMS data, and WhatsApp name historical past for any cellphone quantity in change for fee.
- We recognized and reported 28 CallPhantom apps on Google Play, cumulatively downloaded greater than 7.3 million occasions.
- Some CallPhantom apps sidestep Google Play’s official billing system, complicating victims’ refund efforts.
Investigation
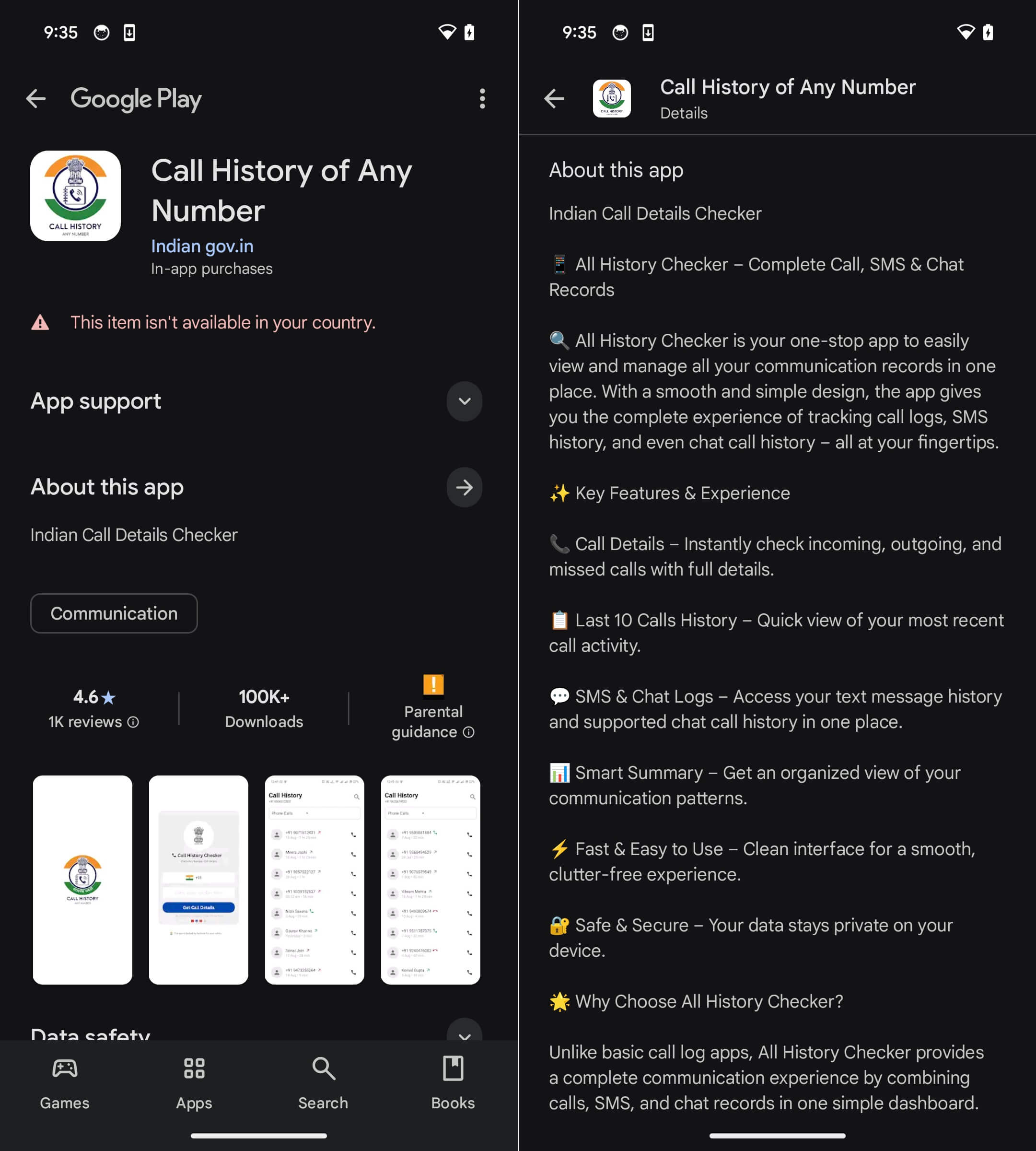
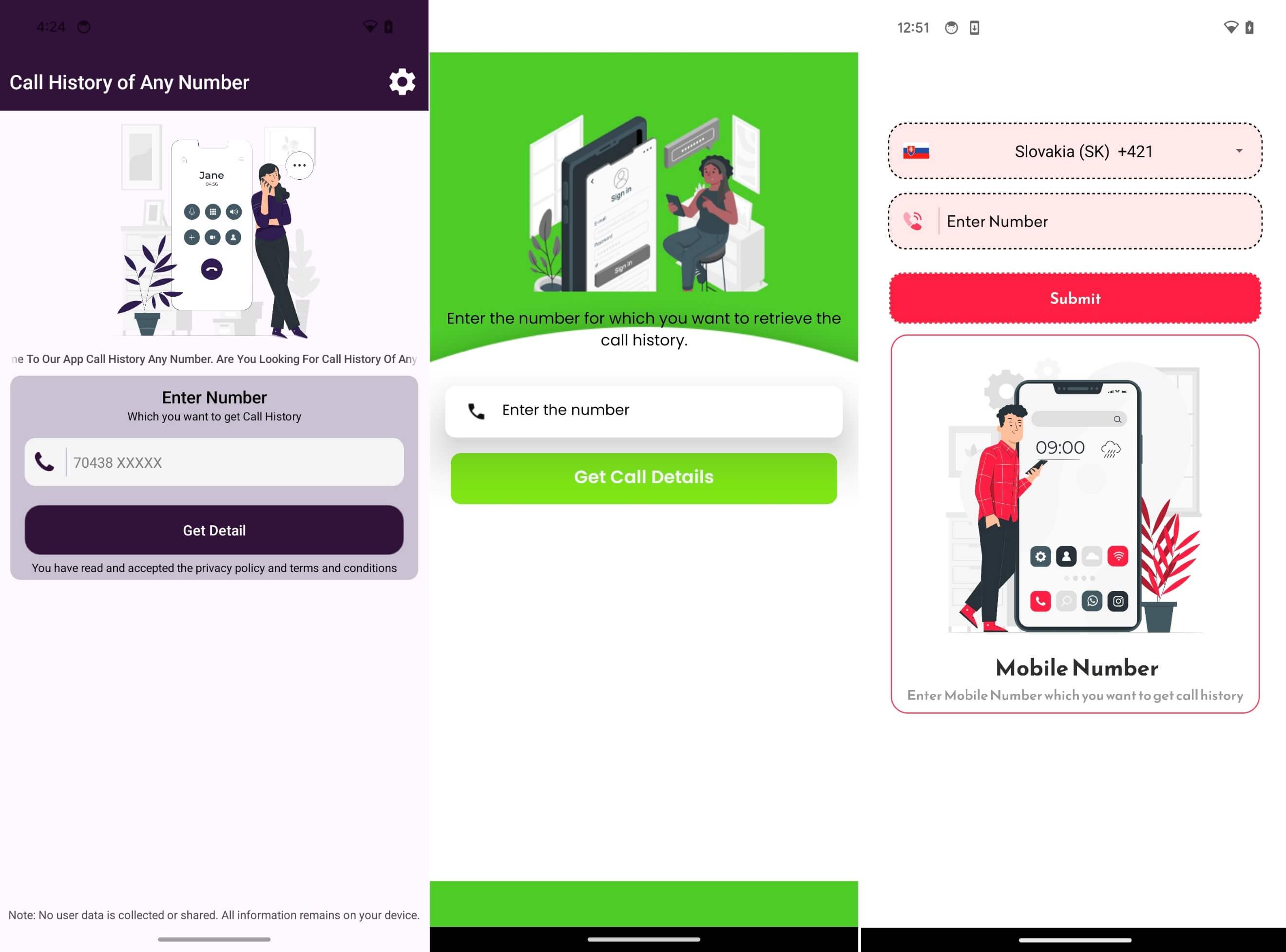
In November 2025, we got here throughout a Reddit publish discussing an app named Name Historical past of Any Quantity, discovered on Google Play. The app, proven in Determine 1, claims that it will probably retrieve the decision historical past of any cellphone quantity equipped by the consumer. It was printed beneath the developer title Indian gov.in, however the app has no actual affiliation with the Indian authorities.
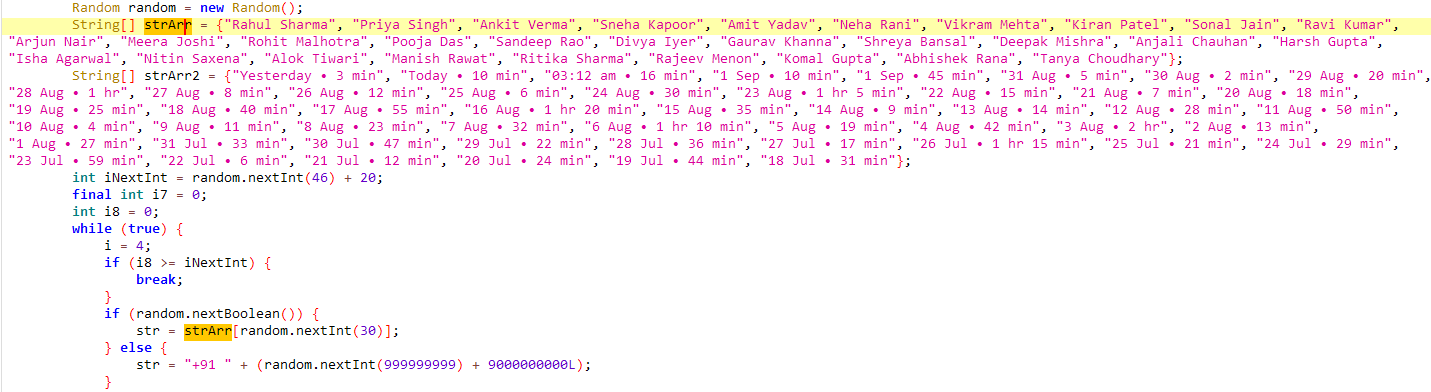
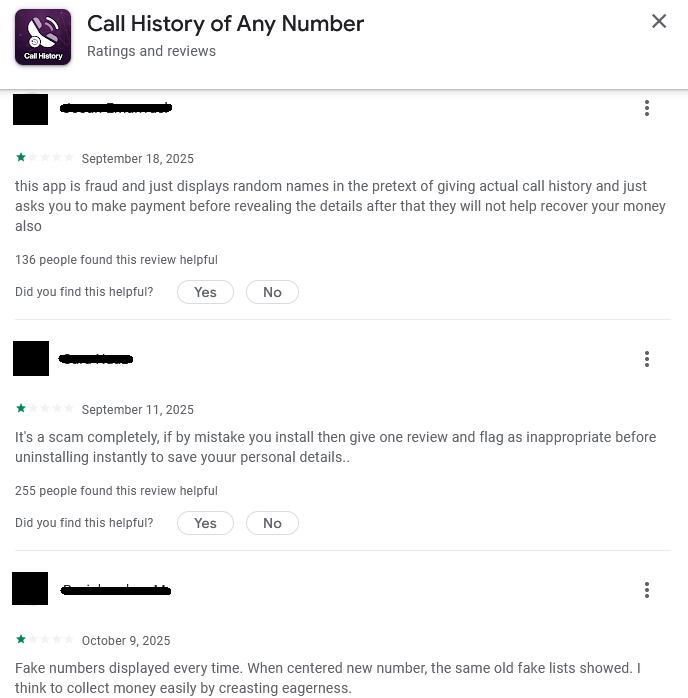
Unsurprisingly, our evaluation confirmed that the “name historical past” knowledge supplied by this app is totally fabricated – the app generates random cellphone numbers and matches them with fastened names, name occasions, and name durations, which have been embedded instantly within the code, as proven in Determine 2. This pretend knowledge is then offered to victims – however solely after fee.
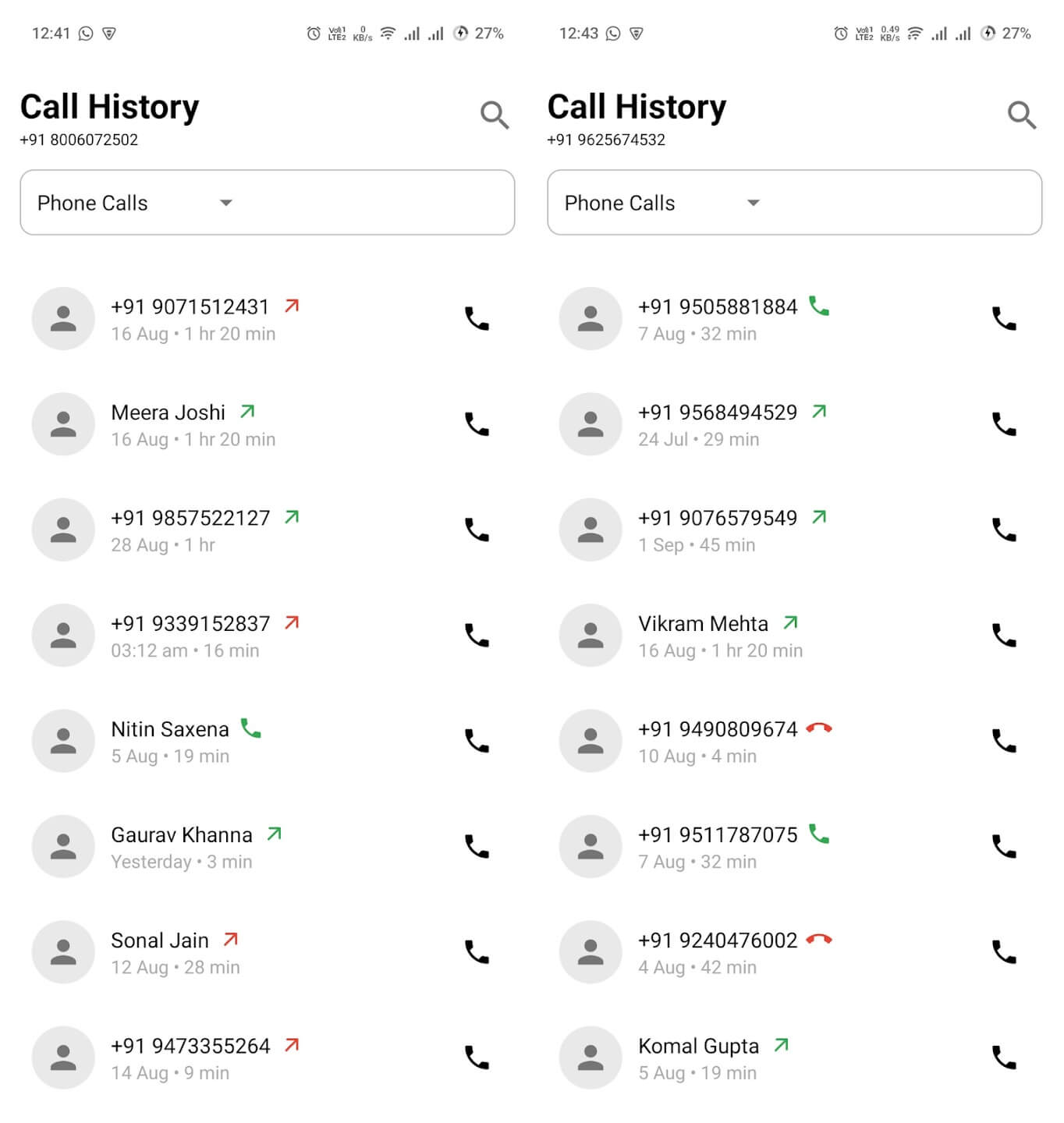
A screenshot of the fabricated name historical past knowledge was even included within the app’s itemizing, offered as an illustration of the app’s performance, as proven in Determine 3.
Additional analysis revealed further, associated apps accessible on the Play Retailer – 28 CallPhantom apps altogether. We reported the complete set of fraudulent apps to Google on December 16th, 2025. On the time of publication, all of the reported apps have been faraway from the shop.
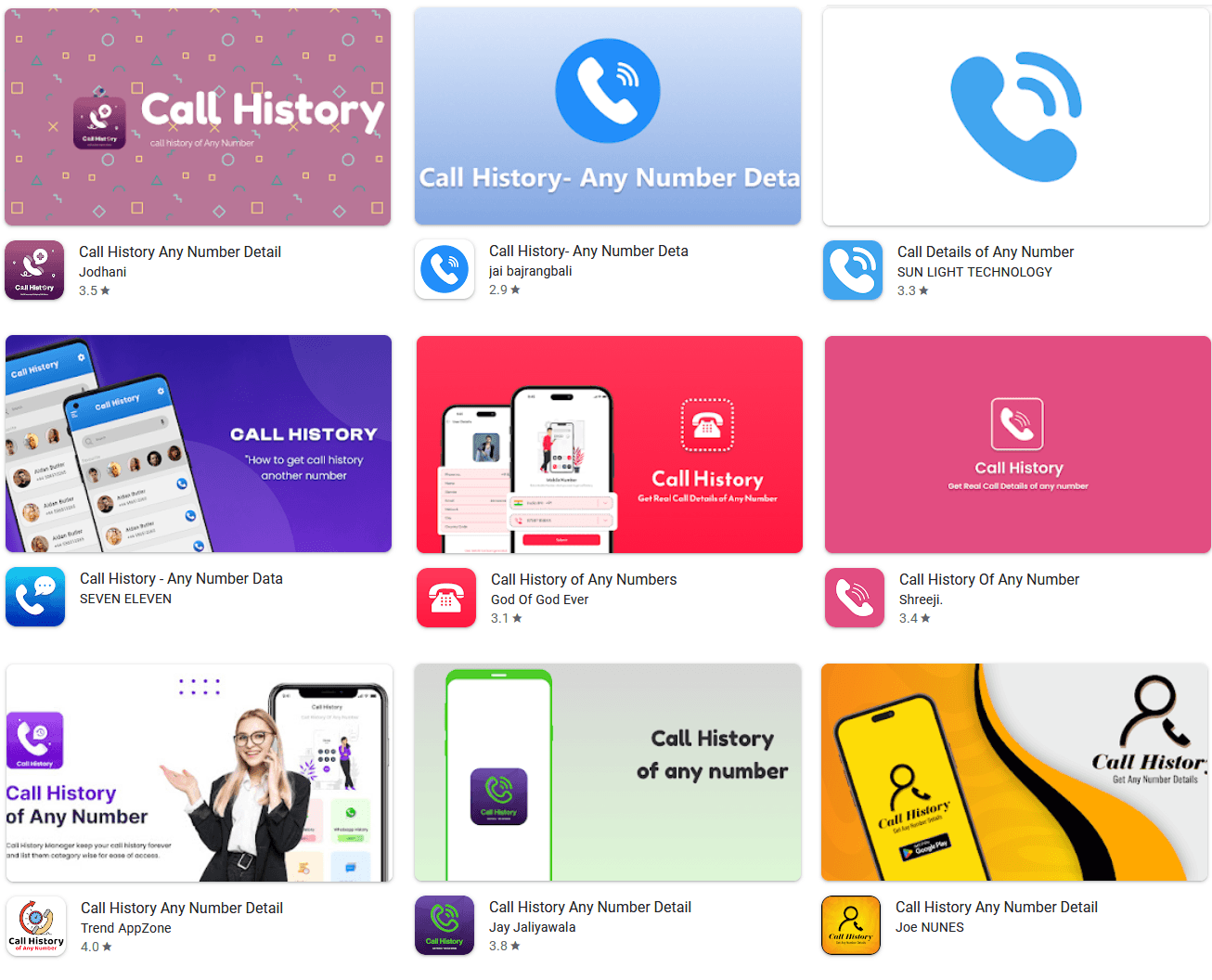
Regardless of visible variations, which will be seen in Determine 4 and Determine 5, the aim of the apps is an identical: generate pretend communication knowledge and cost victims for entry. The desk within the Analyzed CallPhantom apps part lists every app together with its key particulars, together with the obtain rely.
Marketing campaign overview
The CallPhantom apps we discovered on Google Play primarily focused Android customers in India and the broader Asia‑Pacific area. Most of the apps got here with India’s +91 nation code preselected and assist UPI, a fee system used primarily in India.
The apps had garnered quite a few destructive opinions, with victims reporting that they have been scammed and by no means acquired the promised knowledge, as will be seen in Determine 6.
It’s not clear how the apps have been distributed or promoted. Presumably, by seemingly providing perception into non-public info, the scammers efficiently took benefit of individuals’s curiosity. Mixed with just a few glowing (pretend) opinions, it may need appeared like an intriguing provide.
CallPhantom overview
In our investigation, we recognized two important clusters of those fraudulent apps.
The apps within the first cluster include hardcoded names, nation codes, and templates of their code, as proven in Determine 7. These are mixed with randomly generated cellphone numbers and proven to the consumer as partial “outcomes”. To view the complete (pretend) historical past, the sufferer has to pay.
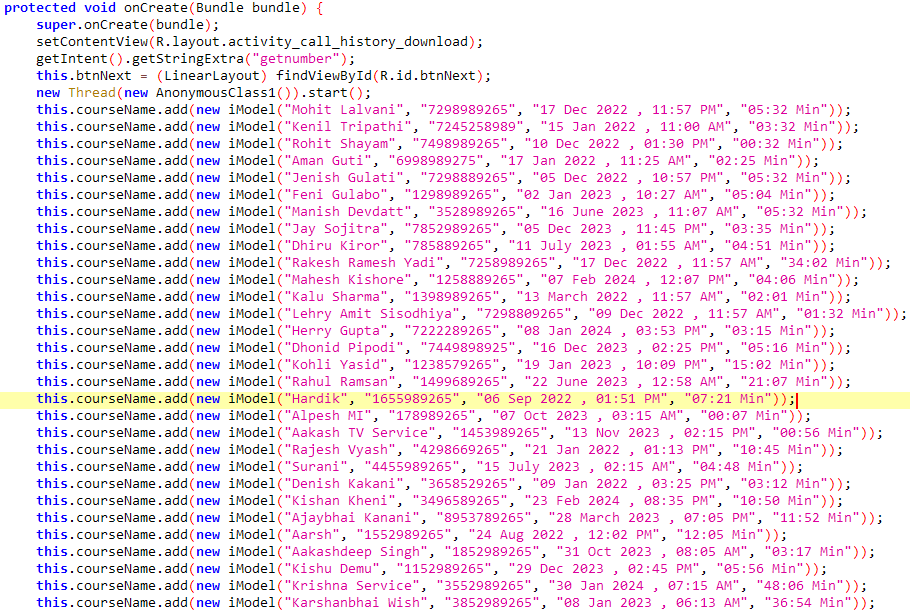
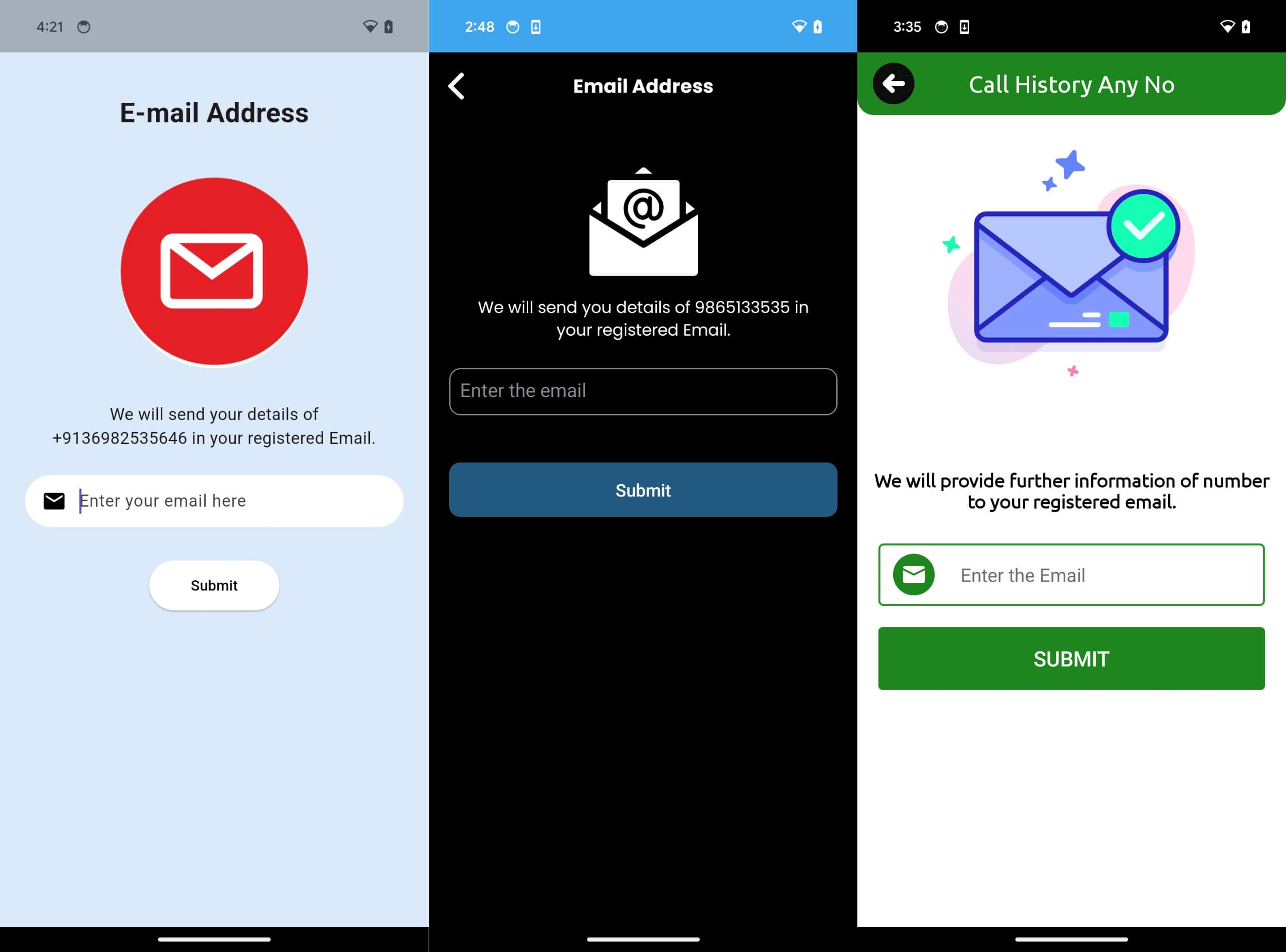
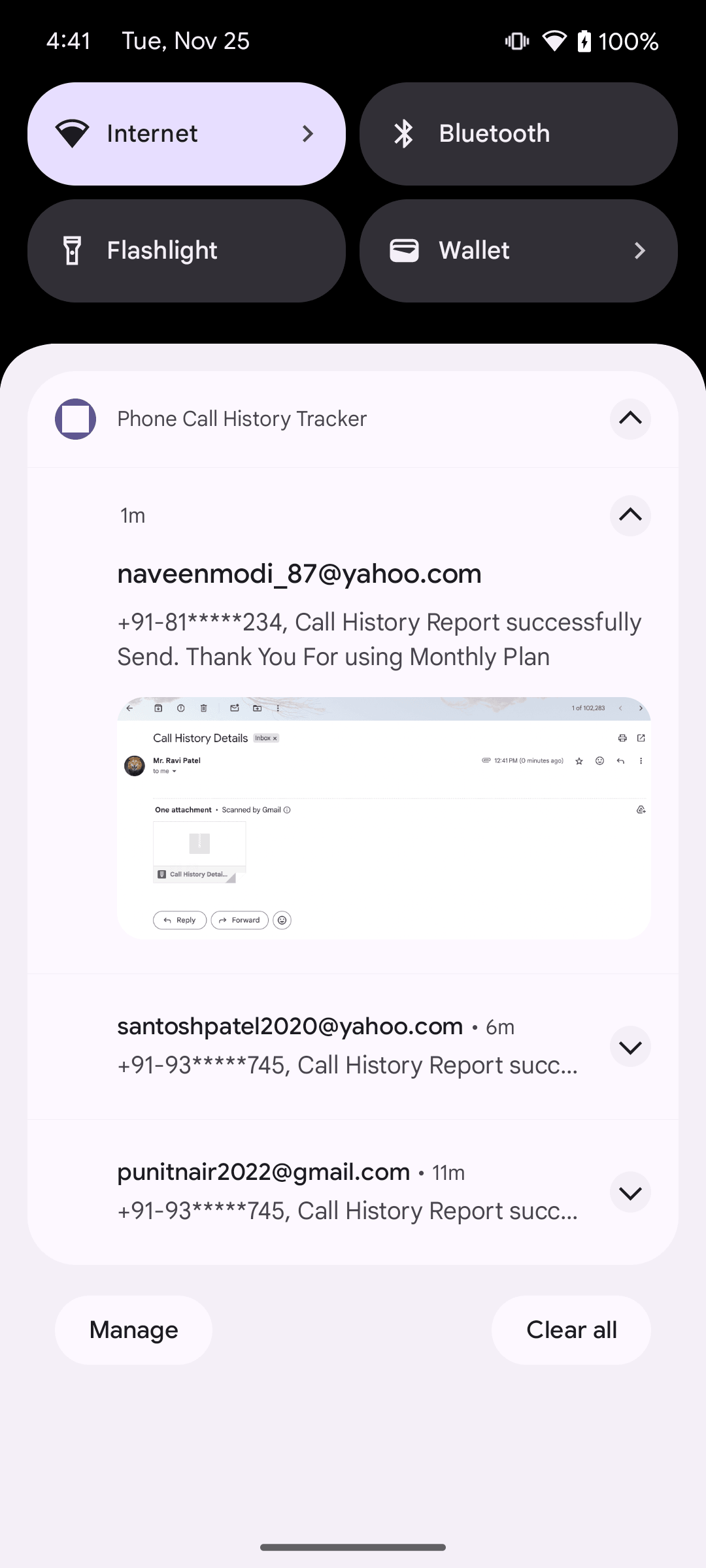
The apps within the second cluster ask customers to enter an e mail deal with the place the “retrieved” name historical past would supposedly be delivered, as seen within the screenshots in Determine 8. No knowledge era happens till after fee; customers must pay or subscribe earlier than any e mail would supposedly be despatched.
On the whole, CallPhantom apps have a easy consumer interface and don’t request any intrusive or delicate permissions – they don’t must. Coincidentally, they don’t include any performance able to retrieving actual name, SMS, or WhatsApp knowledge.
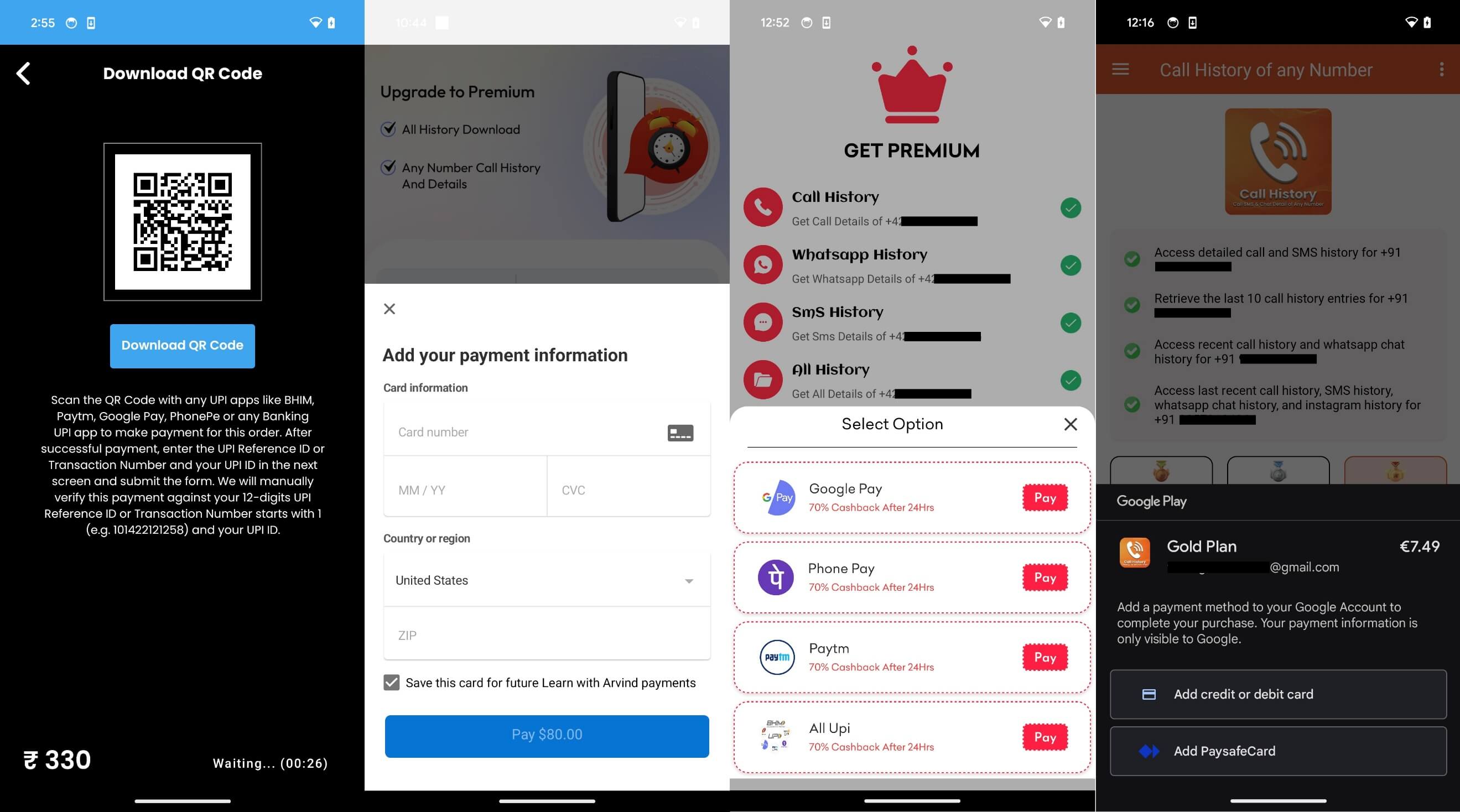
Within the CallPhantom apps we analyzed, we noticed three totally different fee strategies used, the latter two of that are in violation of Google Play’s funds coverage.
First, a few of the apps relied on subscriptions by way of Google Play’s official billing system. That is required of apps providing in-app purchases, per Google Play’s funds coverage; such purchases are lined by Google’s refund safety.
Second, a few of the apps relied on funds by way of third-party apps that assist UPI. For these third-party fee apps, CallPhantom apps both included hardcoded URLs or fetched the URLs dynamically from a Firebase realtime database, which means the fee account could possibly be modified at any time by the operator.
Third, in some instances, fee card checkout kinds have been included instantly within the CallPhantom apps.
Examples of the fee strategies will be seen in Determine 9.
In a single case, we noticed an extra tactic used to coax the consumer into paying: if the consumer exited the app with out fee, the app displayed misleading alerts styled as new emails claiming that the decision historical past outcomes had arrived – see Determine 10. Clicking the notification led straight to a subscription display.
The charges requested for the pretend service differ broadly throughout the apps. The apps additionally seem to supply totally different subscription packages, comparable to weekly, month-to-month, or yearly providers, with the best requested value sitting at US$80. For the bottom “subscription tier”, the typical requested value was €5.
What to do when you have been scammed
On the whole, subscriptions bought by means of the official Google Play billing system will be canceled within the Play Retailer app by tapping your profile icon, navigating to Funds & subscriptions → Subscriptions, deciding on the energetic subscription, and tapping Cancel subscription. Google explains the complete course of on its Cancel, pause, or change a subscription on Google Play web page.
For the 28 apps described on this blogpost, present subscriptions have been canceled when the apps have been faraway from Google Play.
In some instances, refunds for Google Play purchases are attainable. Google might subject a refund relying on the time since buy, the kind of merchandise, and its refund coverage. On the whole, requests should be made inside the allowed refund window as described on Google’s assist web page.
If the acquisition was made outdoors Google Play – for instance, by coming into fee card particulars contained in the app or by paying by means of third‑social gathering providers – then Google can’t cancel the subscription or subject a refund, and customers must contact the fee supplier or the app developer instantly.
Conclusion
We recognized a brand new cluster of fraudulent Android apps on Google Play that collectively amassed over 7.3 million downloads earlier than being taken down upon notification by ESET. These apps, which we collectively named CallPhantom, falsely promise to retrieve name logs, SMS data, and WhatsApp name historical past for any cellphone quantity, a technically inconceivable declare designed solely to use folks’s curiosity and mislead them into paying.
Most of the apps circumvented Google Play’s official billing system, pushing customers towards third‑social gathering funds or direct card entry, complicating refund efforts and exposing victims to monetary threat.
Our evaluation revealed that the “outcomes” proven to victims are totally fabricated, usually utilizing hardcoded Indian numbers, predefined names, and generated timestamps disguised as actual communication knowledge.
Customers who subscribed by way of official Google Play billing could also be eligible for refunds beneath Google’s refund insurance policies. Purchases made by way of third‑social gathering fee apps or by means of direct fee card entry can’t be refunded by Google, leaving customers depending on exterior fee suppliers or builders.
For any inquiries about our analysis printed on WeLiveSecurity, please contact us at threatintel@eset.com.ESET Analysis affords non-public APT intelligence reviews and knowledge feeds. For any inquiries about this service, go to the ESET Risk Intelligence web page.
Analyzed CallPhantom apps
| App title | Package deal title | Variety of downloads |
| Name historical past : any quantity deta | calldetaila.ndcallhisto.rytogetan.ynumber | 3M+ |
| Name Historical past of Any Quantity | com.pixelxinnovation.supervisor | 1M+ |
| Name Particulars of Any Quantity | com.app.name.element.historical past | 1M+ |
| Name Historical past Any Quantity Element | sc.name.ofany.mobiledetail | 500K+ |
| Name Historical past Any Quantity Element | com.cddhaduk.callerid.block.contact | 500K+ |
| Name Historical past Of Any Quantity | com.basehistory.historydownloading | 500K+ |
| Name Historical past of Any Numbers | com.name.of.any.quantity | 100K+ |
| Name Historical past Of Any Quantity | com.rajni.callhistory | 100K+ |
| Name Historical past Any Quantity Element | com.callhistory.calldetails.callerids.calle |
100K+ |
| Name Historical past Any Quantity Element | com.callinformative.instantcall |
100K+ |
| Name Historical past Any Quantity element | com.name.element.caller.historical past | 100K+ |
| Name Historical past Any Quantity Element | com.anycallinformation.datadetailswho.calli |
100K+ |
| Name Historical past Any Quantity Element | com.callhistory.callhistoryyourgf | 100K+ |
| Name Historical past Any Quantity | com.calldetails.smshistory.callhistoryofany |
50K+ |
| Name Historical past Any Quantity Element | com.callhistory.anynumber.chapfvor.historical past | 50K+ |
| Name Historical past of Any Quantity | com.callhistory.callhistoryany.name | 50K+ |
| Name Historical past Any Quantity Element | com.title.issue | 50K+ |
| Name Historical past Of Any Quantity | com.getanynumberofcallhistory.callhistoryof |
50K+ |
| Name Historical past Of Any Quantity | com.chdev.callhistory | 10K+ |
| Telephone Name Historical past Tracker | com.cellphone.name.historical past.tracker | 10K+ |
| Name Historical past- Any Quantity Deta | com.pdf.maker.pdfreader.pdfscanner | 10K+ |
| Name Historical past Of Any Quantity | com.any.numbers.calls.historical past | 10K+ |
| Name Historical past Any Quantity Element | com.callapp.historyero | 1K+ |
| Name Historical past – Any Quantity Knowledge | all.callhistory.element | 500+ |
| Name Historical past For Any Quantity | com.easyranktools.callhistoryforanynumber | 100+ |
| Name Historical past of Numbers | com.sbpinfotech.findlocationofanynumber | 100+ |
| Name Historical past of Any Quantity | callhistoryeditor.callhistory.numberdetails |
50+ |
| Name Historical past Professional | com.all_historydownload.anynumber.callhisto |
50+ |
IoCs
A complete checklist of indicators of compromise (IoCs) and samples will be present in our GitHub repository.
Information
SHA-1
Filename
Detection
Description
799BB5127CA54239D3D4
all.callhistory.deta
Android/CallPhantom.Okay
Android CallPhantom.
56A4FD71D1E4BBA2C5C2
calldetaila.ndcallhi
Android/CallPhantom.M
Android CallPhantom.
EC5E470753E76614CD28
callhistoryeditor.ca
Android/CallPhantom.F
Android CallPhantom.
77C8B7BEC79E7D9AE0D0
com.all_historydownl
Android/CallPhantom.G
Android CallPhantom.
9484EFD4C19969F57AFB
com.any.numbers.name
Android/CallPhantom.L
Android CallPhantom.
CE97CA7FEECDCAFC6B8E
com.anycallinformati
Android/CallPhantom.B
Android CallPhantom.
FC3BA2EDAC0BB9801F85
com.app.name.element.
Android/CallPhantom.N
Android CallPhantom.
B7B80FA34A41E3259E37
com.basehistory.hist
Android/CallPhantom.O
Android CallPhantom.
F0A8EBD7C4179636BE75
com.name.element.name
Android/CallPhantom.C
Android CallPhantom.
D021E7A0CF45EECC7EE8
com.name.of.any.numb
Android/CallPhantom.Q
Android CallPhantom.
04D2221967FFC4312AFD
com.callapp.historye
Android/CallPhantom.E
Android CallPhantom.
CB31ED027FADBFA3BFFD
com.calldetails.smsh
Android/CallPhantom.Q
Android CallPhantom.
C840A85B5FBAF1ED3E0F
com.callhistory.anyn
Android/CallPhantom.J
Android CallPhantom.
BB6260CA856C37885BF9
com.callhistory.name
Android/CallPhantom.S
Android CallPhantom.
55D46813047E98879901
com.callhistory.name
Android/CallPhantom.T
Android CallPhantom.
E23D3905443CDBF4F1B9
com.callhistory.name
Android/CallPhantom.D
Android CallPhantom.
89ECEC01CCB15FCDD2F6
com.callinformative.
Android/CallPhantom.B
Android CallPhantom.
8EC557302145B40FE089
com.cddhaduk.calleri
Android/CallPhantom.U
Android CallPhantom.
6F72FF58A67EF7AAA79C
com.easyranktools.ca
Android/CallPhantom.H
Android CallPhantom.
28D3F36BD43D48F02C50
com.getanynumberofca
Android/CallPhantom.D
Android CallPhantom.
47CEE9DED41B953A84FC
com.chdev.callhistor
Android/CallPhantom.V
Android CallPhantom.
9199A376B433F888AFE9
com.title.issue.apk
Android/CallPhantom.P
Android CallPhantom.
053A6A723FA2BFDA8A1B
com.pdf.maker.pdfrea
Android/CallPhantom.W
Android CallPhantom.
4B537A7152179BBA19D6
com.cellphone.name.histo
Android/CallPhantom.I
Android CallPhantom.
87F6B2DB155192692BAD
com.pixelxinnovation
Android/CallPhantom.X
Android CallPhantom.
583D0E7113795C7D6868
com.rajni.callhistor
Android/CallPhantom.Y
Android CallPhantom.
45D04E06D8B329A01E68
com.sbpinfotech.discover
Android/CallPhantom.A
Android CallPhantom.
34393950A950F5651F3F
sc.name.ofany.cell
Android/CallPhantom.Z
Android CallPhantom.
Community
| IP | Area | Internet hosting supplier | First seen | Particulars |
| 34.120.160[.]131 |
call-history-7cda4-defau call-history-ecc1e-defau |
Google LLC | 2025‑05‑14 | CallPhantom C&C server. |
| 34.120.206[.]254 |
ch-ap-4-default-rtdb.fir chh1-ac0a3-default-rtdb.
|
Google LLC | 2025‑04‑17 | CallPhantom C&C server. |
MITRE ATT&CK strategies
This desk was constructed utilizing model 18 of the MITRE ATT&CK framework.
| Tactic | ID | Identify | Description |
| Command and Management | T1437.001 | Software Layer Protocol: Net Protocols | CallPhantom makes use of Firebase Cloud Messaging for C&C communication. |
| Affect | T1643 | Generate Site visitors from Sufferer | CallPhantom tries to realize fraudulent billing. |










