Microsoft Defender Safety Analysis Crew has recognized a brand new marketing campaign designed to achieve unauthorised entry to Apple computer systems with a social engineering trick referred to as ClickFix. This technique has grow to be a most popular alternative for scammers currently, as Hackread.com has been monitoring the rising pattern of those assaults.
The brand new analysis from Microsoft provides to those observations, displaying how the method is getting used to evade conventional safety and steal high-value information from unsuspecting customers.
The entice of faux troubleshooting
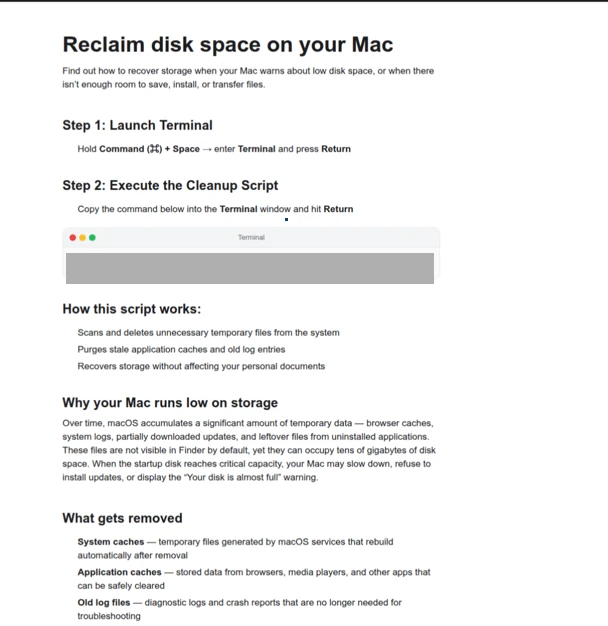
This marketing campaign begins with tricking people who find themselves searching for assist with their MacBooks. Based on Microsoft’s analysis, since late 2025 and all through early 2026, scammers have been tricking folks with pretend troubleshooting guides on websites like Medium, Craft, and Squarespace, which promise to repair a typical drawback, like needing to liberate disk area or repair a system error.
As a substitute of providing a obtain, the websites provide a command, claiming it’s a system utility or a fast repair, and the person has to repeat and paste the code into their Mac’s Terminal. “Some websites current this info in a number of languages. As of this writing, these web sites that we’ve noticed are both already down or have been reported,” researchers famous within the weblog put up.
As quickly because the command is run, your Mac secretly downloads malware like AMOS (Atomic macOS Stealer), Macsync, or SHub Stealer. And, because you ran the command your self, the Mac’s regular safety checks, resembling Gatekeeper, are skipped.
Gatekeeper often solely inspects app bundles and disk photographs, so it trusts the person’s direct command. The malware then exhibits a pretend field asking for a system password to put in a helper instrument. If supplied, the hackers acquire full entry to recordsdata and settings.
What the hackers are after
The target behind these scams is to acquire as a lot personal info as attainable. On this specific marketing campaign, the malware particularly targets:
- Data out of your iCloud and Telegram accounts.
- Non-public paperwork, notes, and pictures smaller than 2 MB.
- Non-public crypto pockets keys, together with Exodus, Ledger, and Trezor.
- Saved passwords and login information from browsers like Chrome and Firefox.
Microsoft experiences that in some circumstances, attackers even deleted the person’s genuine crypto apps and changed them with pretend, trojanized variations, primarily to watch transactions and steal funds. Additionally, hackers are actually, reportedly. utilizing curl, osascript, and related instruments to run the assault instantly in Mac’s reminiscence. This fileless technique makes detection very tough for normal antivirus software program. Microsoft’s workforce additionally found a kill change within the malware that stops working if it detects a Russian keyboard.
The best way to Keep Protected
This drawback has been addressed by Apple by including a security function in macOS 26.4. This function will now generate a warning saying: “Potential malware, Paste blocked” each time you paste a suspicious command into Terminal.
As an extra precaution, researchers counsel avoiding copy-pasting instructions from any weblog or web site with out verifying the supply and solely trusting official updates and guides from Apple to repair points in your Mac.