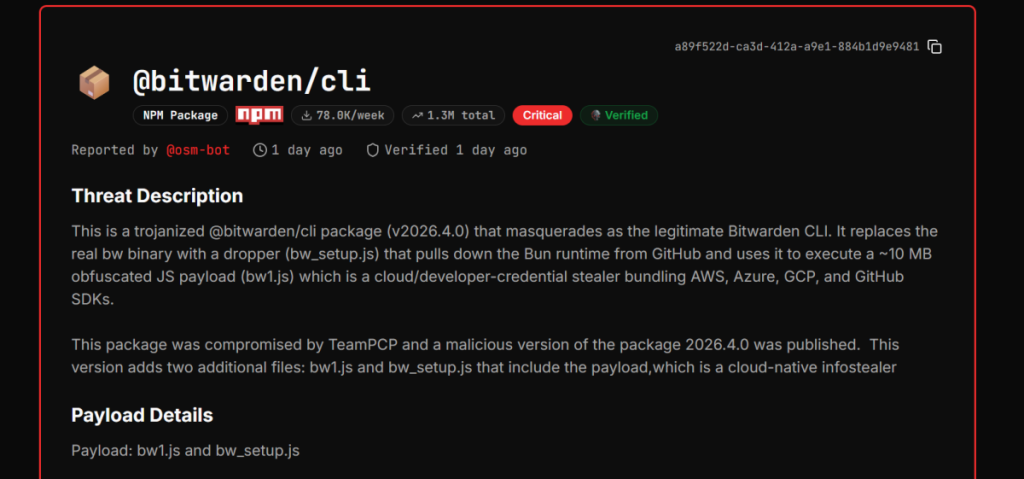
On April 20, 2026, at round 5:00 pm CET, the coding world was alerted after a broadly used software known as @bitwarden/cli was discovered to be compromised. In keeping with researchers at GitGuardian, who shared their evaluation with Hackread.com, the assault was a calculated operation by a gaggle known as TeamPCP, who used what researchers describe as a cross-campaign pivot to use trusted developer instruments.
For context, Bitwarden is an open-source password supervisor that shops and encrypts delicate knowledge like passwords, API keys, and safe notes in a protected vault, accessible throughout units. It makes use of end-to-end encryption so solely the consumer can learn their knowledge.
The Bitwarden CLI is a command-line interface that lets builders work together with the vault immediately from a terminal, typically utilized in scripts, automation, and CI pipelines to retrieve secrets and techniques. The Bitwarden CLI package deal, usually distributed through npm as @bitwarden/cli, is the installable model of this software, making it straightforward for builders to combine safe credential entry into improvement workflows.
The Return of Shai Hulud
The hackers used a self-propagating worm generally known as Shai-Hulud (additionally tracked as CanisterSprawl). Most malware fails when its dwelling base is blocked, however this one has a backup plan. Researchers famous that if the malware can’t attain its main web site, auditcheckmarxcx, it makes use of GitHub itself as a fallback C2 (command and management) server. It searches public GitHub commits for a particular tag: LongLiveTheResistanceAgainstMachines.
Additional investigation revealed that these public posts contained secret PATs (Private Entry Tokens) and new directions. In a single occasion, the hackers used a repository named helloworm00/hello-world to broadcast a brand new exfiltration area: safely-irc-weblogs-fewtrycloudflarecom.
The malware then creates a brand new repository beneath the sufferer’s personal GitHub account to add encrypted credential blobs. This strategy makes the theft appear like regular developer exercise.
Focusing on AI Assistants
Shai-Hulud can also be designed to poison AI coding assistants. It scans the system for six particular instruments: Claude Code, Gemini CLI, Codex CLI, Kiro CLI, Aider, and OpenCode. If discovered, the malware injects a 3,500-byte heredoc block (a technique of inserting a big chunk of code immediately right into a script) into the ~/.bashrc and ~/.zshrc recordsdata.
These recordsdata, to your data, function a startup script for the pc’s command line. So, this step is essential as a result of by injecting code right here, the malware ensures it runs robotically each time a developer opens their terminal.
Uncommon Discovery
A stunning discovering is that the preliminary entry vector was Dependabot, a trusted automation bot constructed into GitHub. This software robotically fetched a trojanized Checkmarx KICS Docker picture (particularly the checkmarx/kics:newest tag) on April 22, 2026.
“One confirmed sufferer atmosphere exhibits the assault started with the Checkmarx KICS Docker picture compromise on April 22, 2026. Dependabot pulled the trojanized checkmarx/kics:newest tag throughout an automatic dependency replace, executing the payload in CI with entry to repository secrets and techniques. This confirms the cross-campaign pivot that TeamPCP has used all through this wave: compromise a trusted CI software, harvest runner credentials, use these credentials to propagate additional,” the report reveals.
This was notably tough for researchers to cease. That’s as a result of Dependabot is a trusted, automated system designed to extend safety; nonetheless, right here it was used to bypass human evaluate totally. Because it runs with elevated CI (Steady Integration) permissions, the hackers have been capable of steal repository secrets and techniques with zero human intervention.
“This isn’t a developer manually putting in one thing sketchy,” Lead researcher Guillaume Valadon famous within the weblog publish, explaining that as a result of Dependabot ran robotically, “nobody was watching.” This allowed the menace actors to steal credentials and propagate the assault additional.
To forestall future incidents, researchers suggest that firms apply a cooldown interval earlier than putting in new dependency updates to offer the safety neighborhood sufficient time to search out and flag any hidden malware earlier than it reaches your system.