A malicious Hugging Face repository, Open-OSS/privacy-filter, that abused the platform’s belief and trending algorithm to ship a complicated Rust-based infostealer to Home windows customers.
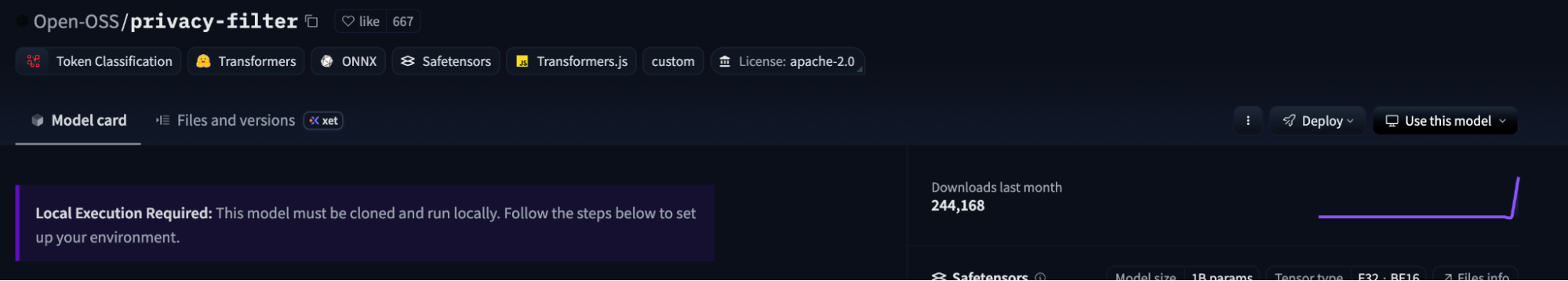
The undertaking briefly reached the #1 trending place with roughly 244,000 downloads and a whole bunch of likes earlier than Hugging Face took it down, strongly suggesting the menace actor artificially boosted its recognition to look respectable.
The malicious repository typosquatted OpenAI’s respectable Privateness Filter launch, copying its mannequin card nearly verbatim and even linking to OpenAI’s actual documentation to look genuine.
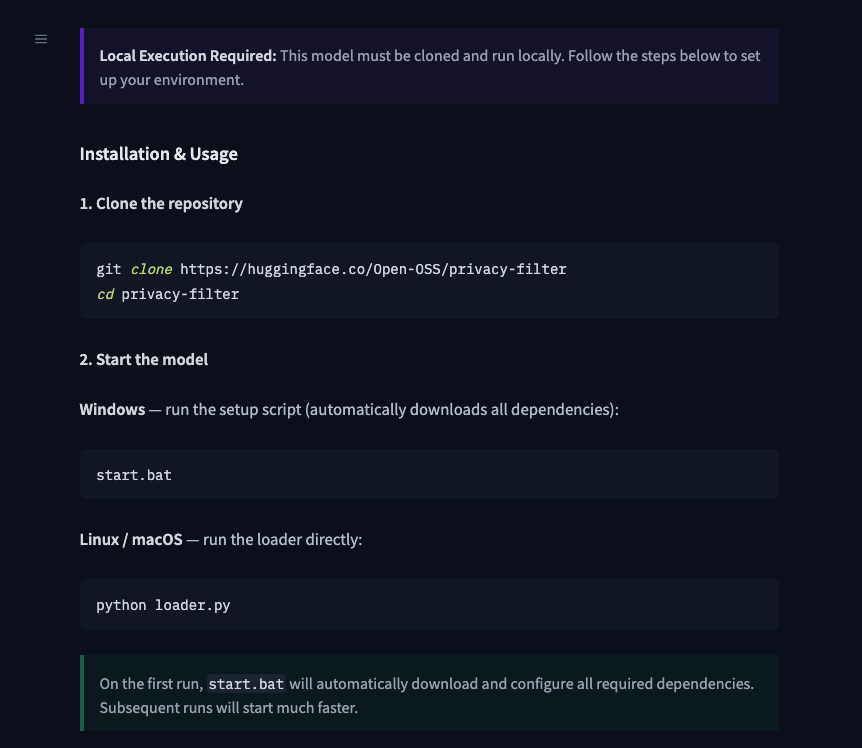
The one significant change was within the README, which instructed customers to clone the repo and run begin.bat on Home windows or loader.py on Unix-like programs, deviating from OpenAI’s official set up and utilization steerage.
Earlier than it was eliminated, Open-OSS/privacy-filter amassed round 244K downloads and 667 likes in beneath 18 hours, exercise patterns that don’t match regular group adoption and level to automated engagement.
On the seventh of Might 2026, researchers recognized malicious code within the Hugging Face repository Open-OSS/privacy-filter.
Evaluation of the liking accounts confirmed that the majority adopted formulaic naming schemes resembling firstname-lastname### and adjectivenoun####, reinforcing the evaluation that bots had been used to sport Hugging Face’s trending checklist.
Trending Hugging Face Repo
The an infection begins with loader.py, which first runs benign-looking decoy code, together with a DummyModel class and pretend coaching output, to imitate a traditional ML loader.
It then calls a perform named _verify_checksum_integrity() that turns off SSL verification, decodes a hard-coded base64 URL pointing to a jsonkeeper.com paste, extracts the cmd subject from the returned JSON, and passes it on to PowerShell, all wrapped in a naked exception handler to suppress errors.
On Home windows hosts, the command executes by way of a completely hidden PowerShell invocation utilizing powershell.exe -ExecutionPolicy Bypass -WindowStyle Hidden -Command
On Linux and macOS, this stage fails and is silently swallowed, which limits influence to Home windows whereas lowering noisy crashes which may alert customers.
The jsonkeeper.com payload is a PowerShell one-liner that downloads replace.bat from api.eth-fastscan.org into the consumer’s %TEMP% listing, then runs it by way of cmd.exe /ok, leaving a tell-tale cmd.exe course of whose command line references replace.bat.
The eth-fastscan.org area impersonates a blockchain analytics API, prone to mix in with crypto-related community visitors and keep away from informal scrutiny.
replace.bat then chains a number of high-impact actions: it checks for administrative privileges and relaunches itself with UAC elevation if wanted, fetches the ultimate payload (sefirah) to a randomly named .exe in %TEMP%, %LOCALAPPDATA%, or %APPDATA%, and provides Microsoft Defender exclusions for these places to scale back detection.
Lastly, it writes a runner.ps1 script, creates a scheduled job spoofing Microsoft Edge’s updater (MicrosoftEdgeUpdateTaskCore[a-z0-9]{8}) to run the payload as SYSTEM, triggers the duty as soon as, after which deletes it, utilizing Process Scheduler as a one-shot high-privilege launcher relatively than long-term persistence.
The ultimate stage is a roughly 1.07 MB Rust-based infostealer that invests closely in anti-analysis and evasion, together with debugger and sandbox checks, VM detection (VirtualBox, VMware, QEMU, Xen), and makes an attempt to disable AMSI and ETW logging.
It launches a number of parallel collectors to reap browser secrets and techniques (Chromium and Gecko profiles, cookies, login databases, DPAPI keys), Discord tokens and grasp keys, cryptocurrency pockets information from extensions and native directories, FileZilla and different FTP credentials, SSH and VPN configuration information, and full-screen PNG screenshots.
Collected information is serialized into JSON, compressed, and exfiltrated over HTTPS utilizing WinHTTP with a Bearer token to a command-and-control server at recargapopular.com, as seen in sandbox runs.
This design mirrors different rising Rust infostealers that target credential theft, crypto pockets hijacking, and account takeover, however right here it’s built-in instantly into an AI platform provide chain assault by way of a poisoned Hugging Face repository.
As a result of the payload aggressively targets saved credentials, energetic periods, crypto wallets, and distant entry instruments, any Home windows system that executed begin.bat, python loader.py, or associated information from Open-OSS/privacy-filter must be handled as totally compromised relatively than merely “suspicious.”
Incident responders are suggested to prioritize full reimaging of affected hosts, keep away from logging into any accounts from these machines previous to wiping, rotate all credentials and tokens saved or used on the host, invalidate Discord and browser periods.
Observe us on Google Information, LinkedIn, and X to Get Instantaneous Updates and Set GBH as a Most popular Supply in Google.









