A extremely evasive multi-stage malware marketing campaign deploying the Vidar Infostealer. First found in late 2018 and constructed on the Arkei stealer supply code, Vidar is infamous for aggressively harvesting consumer credentials, browser session cookies, cryptocurrency wallets, and detailed system information.
Based on an evaluation by researcher Mahadev Joshi, this current marketing campaign makes use of AutoIt scripting and legit platforms to masks its actions and silently talk with command-and-control (C2) servers.
The an infection sequence initiates when a sufferer executes MicrosoftToolkit.exe, a generally abused software program activation device. As an alternative of exploiting system vulnerabilities, the attackers depend on customers willingly downloading and working this utility. As soon as launched, the executable spawns a command shell to start the staging part.
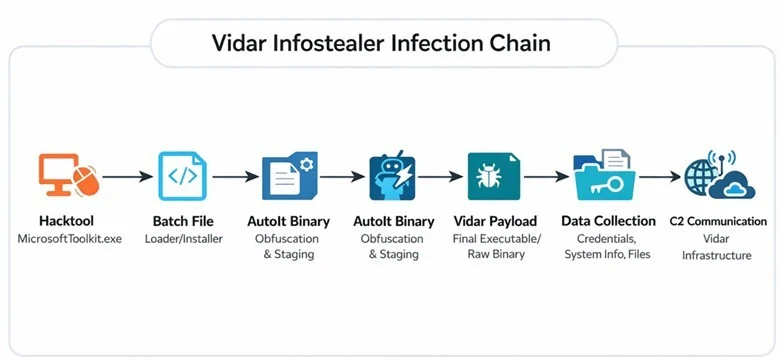
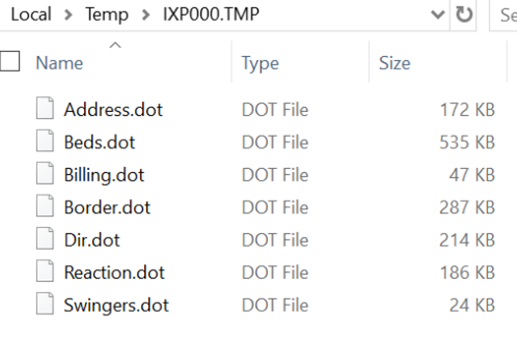
The malware then renames a disguised information file, initially named swingers.dot, right into a batch script. This file extension masquerading permits the malicious script to bypass fundamental safety controls and execute embedded instructions throughout the consumer area with out elevating speedy alarms.
Vidar Infostealer Marketing campaign Steals Passwords
Earlier than dropping its remaining payload, the malware actively maps the native surroundings to keep away from detection. It invokes built-in Home windows instructions like tasklist.exe and findstr.exe to enumerate working processes and try and disrupt energetic safety tooling, as reported by LevelBlue.
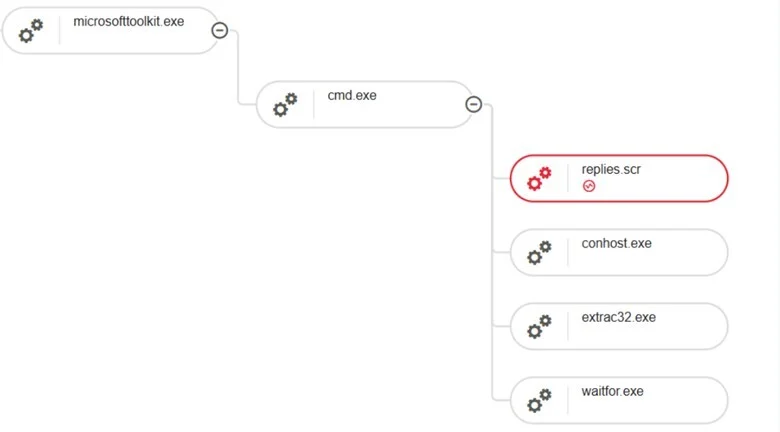
Following this reconnaissance, the malware makes use of extract32.exe to extract secondary payload elements from a number of .dot information. The core of this staging part includes an AutoIt-compiled binary named Replies.scr.
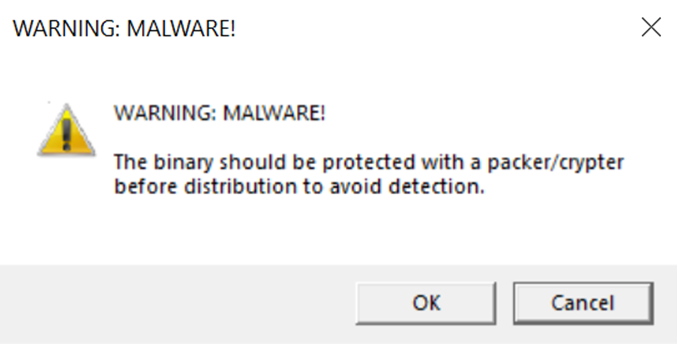
AutoIt is a reputable Home windows automation language, making it an ideal disguise for attackers to run malicious logic with out triggering antivirus signatures. This executable capabilities as a builder-style loader, studying an encrypted exterior payload file into reminiscence for decryption and execution.
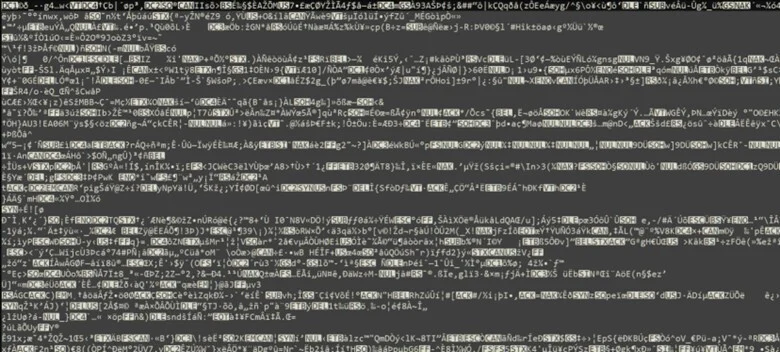
The payload actively resists safety evaluation throughout runtime. It leverages ZwQueryInformationProcess to verify for course of debug flags, successfully pausing or altering the method’s habits if it detects a researcher’s debugger. It additionally checks for instrumentation callbacks usually utilized by Endpoint Detection and Response (EDR) options.
As soon as the Vidar stealer is efficiently loaded into reminiscence, it establishes outbound communication utilizing WinINet-based utility programming interfaces (APIs). The malware retrieves its configuration information and staging directions from public net content material earlier than starting information exfiltration.
The C2 communication technique is especially stealthy as a result of it targets reputable companies. Researchers noticed the malware setting up HTTP GET requests to particular Telegram and Steam Group profile URLs.
By utilizing these trusted platforms as dead-drop resolvers, the malware blends its beaconing exercise with regular net visitors, making network-level detection extremely troublesome. It additionally resolves dynamic domains through public Google DNS earlier than establishing broader outbound connections.
After efficiently exfiltrating information, the preliminary MicrosoftToolkit.exe course of runs an intensive cleanup routine to erase its tracks. The malware resets the attributes of all dropped .dot payload information and systematically deletes them from the disk.

It then frees all related reminiscence buildings, iterates by means of the staging listing to take away remaining execution artifacts, and terminates its personal course of utilizing RtlExitUserProcess.
This self-deletion functionality considerably reduces forensic artifacts on the compromised endpoint, significantly complicating retrospective incident response efforts and permitting the menace actors to stay hidden lengthy after the information theft is full.
IOCs
| IOC | IOC sort | Description |
| fc27479ff929d846e7c5c5d147479c81e483a2ec911bd1501a53aa646a29620d | SHA-256 | MicrosoftToolkit.exe |
| d4fe9f48178cdf375a3be30d17f1dc016b5861dff8683f0bb35a0ba8d44f892f | SHA-256 | swingers.dot.bat |
| 978ad86c90d85b74947bb627ec24f8bcd26812b500e82f5af202160506ac29c6 | SHA-256 | Beds.dot |
| 881619a47b62b52305d92640cc4d4845a279c23a5a749413785fc8fcb0fdf7fb | SHA-256 | replies.scr |
| 968ecf51c442ec0ff91f91689ac524e7e8e9eab0c1a2a65cf13e54cf95194efe | SHA-256 | D (payload file) |
| 149.154.167[.]99 | IP Tackle | Vidar-associated C2 IP |
| telegram[.]me | Area Title | C2 area |
| gz[.]technicalprorj[.]xyz | Area Title | Vidar-associated C2 area |
| Tactic | Methods / Sub-Methods | Abstract |
| TA0001 – Preliminary Entry | T1204.002 – Consumer Execution: Malicious File | Consumer downloaded and executed microsofttoolkit.exe (hacktool), serving because the preliminary entry level into the system |
| TA0002 – Execution | T1204.002 – Consumer Execution: Malicious File | Consumer executed microsofttoolkit.exe, initiating the an infection beneath the belief of reputable software program activation |
| TA0002 – Execution | T1059.003 – Command and Scripting Interpreter: Home windows Command Shell | Batch/script-based execution used to stage additional exercise |
| TA0002 – Execution | T1027 – Obfuscated/Compressed Recordsdata | Payload staged through compressed or embedded format utilizing extract32.exe |
| TA0002 – Execution | T1140 – Deobfuscate/Decode Recordsdata or Data | Extraction course of used to unpack the next-stage payload |
| TA0002 – Execution | T1059 – Command and Scripting Interpreter | AutoIt-based loader executed through script-like habits |
| TA0002 – Execution | T1218 – Signed Binary Proxy Execution | .scr (AutoIt compiled binary) used as a loader to execute malicious logic |
| TA0005 – Protection Evasion | T1036 – Masquerading | A .dot file was renamed to .bat to bypass fundamental file-type restrictions |
| TA0005 – Protection Evasion | T1562.001 – Disable or Modify Safety Instruments | taskkill.exe used to terminate security-related processes |
| TA0005 – Protection Evasion | T1059.003 – Command Shell | findstr.exe leveraged for filtering and figuring out safety processes |
| TA0005 – Protection Evasion | T1070.004 – Indicator Removing on Host: File Deletion | Malware deleted dropped information to take away proof |
| TA0005 – Protection Evasion | T1489 – Service Cease | Processes terminated to scale back forensic artifacts and evade detection |
| TA0011 – Command and Management | T1071.001 – Software Layer Protocol: Net Protocols | Malware communicated with C2 over HTTP/HTTPS |
| TA0011 – Command and Management | T1573 – Encrypted Channel | Encrypted communication used to evade detection |
| TA0010 – Exfiltration | T1041 – Exfiltration Over C2 Channel | Stolen information (credentials, browser information) exfiltrated through C2 channel |
Observe: IP addresses and domains are deliberately defanged (e.g., [.]) to stop unintentional decision or hyperlinking. Re-fang solely inside managed menace intelligence platforms equivalent to MISP, VirusTotal, or your SIEM.
Comply with us on Google Information, LinkedIn, and X to Get Immediate Updates and Set GBH as a Most popular Supply in Google.









