Hackers are abusing GitHub’s personal issue-notification emails to phish builders and silently take over their repositories utilizing malicious OAuth purposes, successfully turning trusted DevOps tooling right into a supply-chain assault vector.
Builders are actually prime targets as a result of compromising their accounts provides attackers direct entry to supply code CI/CD pipelines, and manufacturing workflows, making this a textbook supply-chain assault path.
Attackers begin by creating points on public GitHub repositories that seem like pressing safety alerts, for instance, warning about “uncommon entry makes an attempt” or “malicious commits” tied to the sufferer’s account.
Current campaigns have proven {that a} single malicious OAuth app, pushed at scale, can influence hundreds of repositories in days. By abusing trusted platforms like GitHub, attackers can bypass many conventional e-mail filters and attain builders immediately of their inboxes.
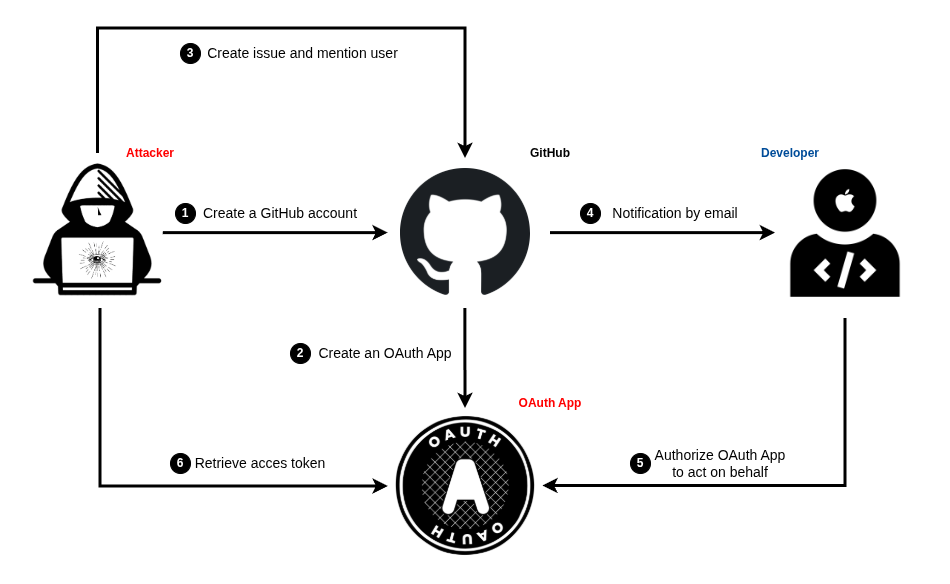
They point out particular usernames within the challenge physique, which routinely triggers a professional notification e-mail from GitHub’s noreply tackle to the goal’s main e-mail.
How GitHub challenge phishing works
The problem textual content is fastidiously formatted with Markdown, mixing daring warnings, pretend detection particulars, and hyperlinks that declare to let the person “evaluation exercise” or “safe the account.”
As a result of these messages originate from GitHub’s personal infrastructure, they move SPF and DKIM checks and look an identical to regular repository notifications, making them arduous to differentiate from actual alerts at a look.
Some attackers additional improve credibility by selecting account and repository names that resemble GitHub safety providers or recognized instruments, in order that the topic line of the e-mail seems reliable.
In some instances, experiences describe a time-of-check time-of-use (TOCTOU) trick, the place the attacker edits or cleans up the difficulty after the notification is shipped, leaving little proof within the repository whereas the sufferer nonetheless has the unique lure of their inbox.
As a substitute of pointing victims to a pretend login web page, the embedded hyperlinks result in a professional github.com OAuth authorization URL for a rogue software managed by the attacker.
On that web page, the app asks for highly effective scopes akin to entry to the person’s e-mail, profile, personal and public repositories, and GitHub Actions workflows, giving the attacker broad management as soon as consent is granted.
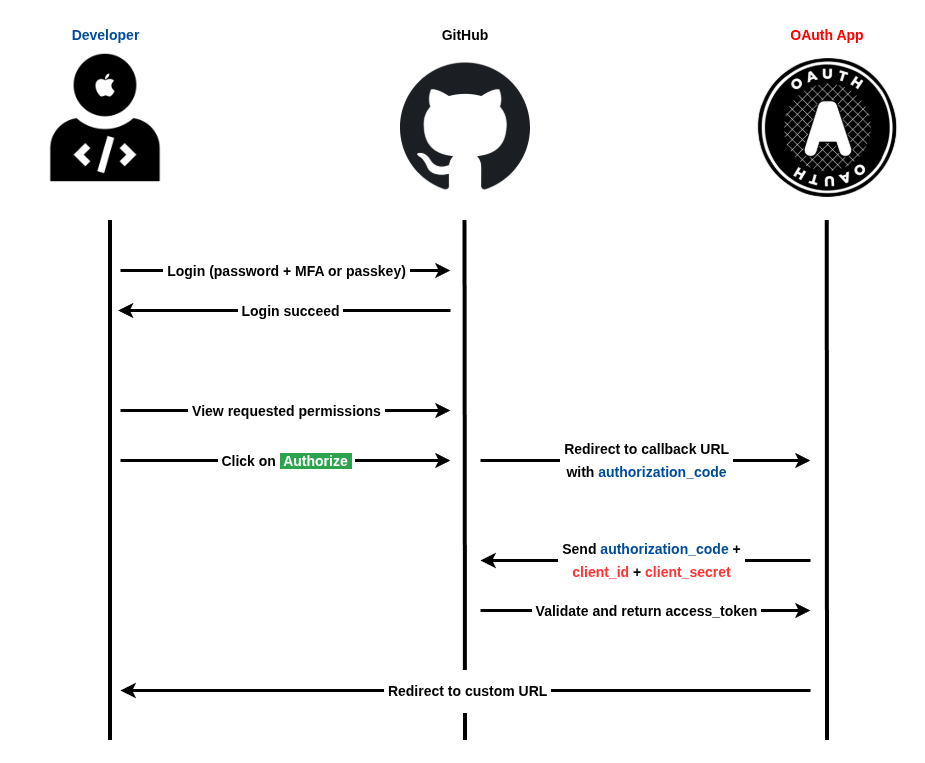
This mannequin, typically referred to as consent phishing, lets risk actors achieve persistent API-level entry with out ever stealing a password or immediately defeating multi-factor authentication.
Malicious OAuth apps and 2FA bypass
As soon as the person clicks “Authorize,” GitHub points an OAuth entry token to the malicious app, which may then clone personal repositories, inject backdoors into code, tamper with workflows, or exfiltrate delicate information.
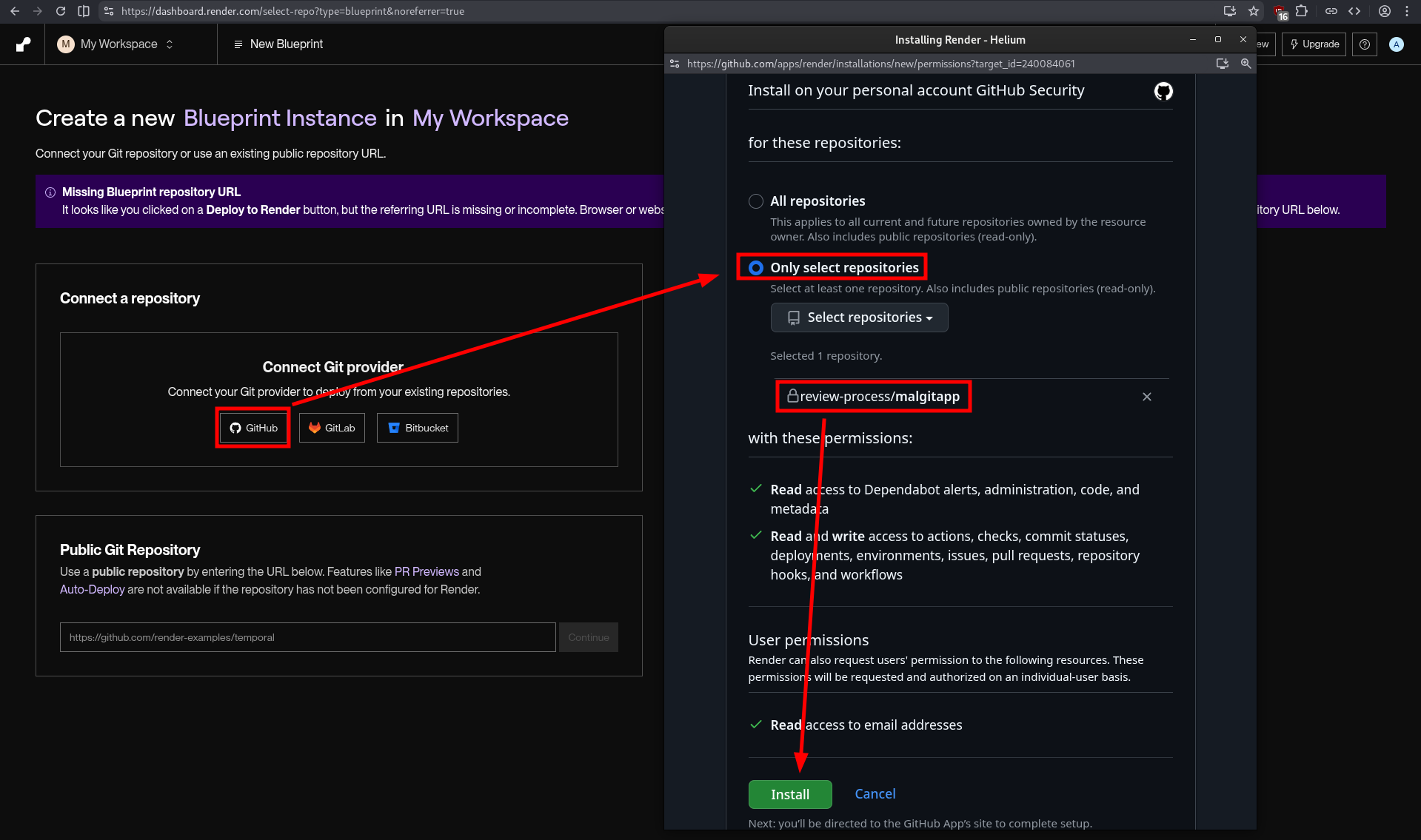
The MalGitApp public repo or fork it in your GitHub phishing account after which join Render to it. Choose solely the specified repositories and click on “Set up”.
Safety researchers have documented campaigns hitting roughly 12,000 repositories with this method, exhibiting how shortly a single malicious app can scale throughout the developer ecosystem.
As a result of all the pieces occurs via official GitHub flows and URLs, many customers don’t understand they’ve handed over entry till suspicious commits or repository exercise seem.
Organizations ought to deal with OAuth app approvals as high-risk occasions and prohibit which apps builders are allowed to authorize, particularly these requesting repo or workflow scopes.
Safety groups ought to frequently evaluation current OAuth grants, revoke unused or suspicious apps, and monitor for uncommon repository modifications tied to tokens moderately than direct logins.
Builders are suggested to confirm any “safety alert” by checking GitHub’s personal safety middle or notifications web page immediately, as a substitute of clicking hyperlinks in emails, and to be cautious of apps that model themselves as safety scanners but demand full repository entry.
Comply with us on Google Information, LinkedIn, and X to Get Prompt Updates and Set GBH as a Most well-liked Supply in Google.










