The panorama of area parking has remodeled dramatically over the previous decade, shifting from a comparatively benign monetization technique to a classy vector for cybercrime.
New analysis into the trendy parking ecosystem reveals a startling actuality: over 90% of holiday makers to parked domains encounter malicious content material, scams, or phishing assaults a stark reversal from situations discovered simply eleven years in the past, when fewer than 5% of parked domains delivered dangerous content material.
Parked domains, as soon as dismissed as bland promoting repositories, have grow to be a main looking floor for menace actors exploiting a fancy ecosystem of area house owners, visitors distribution techniques, and promoting networks.
The transformation displays each deliberate abuse by cybercriminals and unintended vulnerabilities created by legit enterprise practices within the parking business.
The menace from parked domains begins with lookalike domains and customary typos. Throughout analysis into area parking practices, investigators by chance visited ic3.org as an alternative of ic3.gov the FBI’s Web Crime Grievance Middle and have been instantly redirected to a fraudulent “Drive Subscription Expired” rip-off web page.
Underneath completely different circumstances, that very same area might have delivered information-stealing malware or a trojan as an alternative.
What makes this notably harmful is the twin nature of parked domains: when scanned by safety instruments or accessed via VPN companies, they show innocent parking pages, making a false sense of safety.
Actual customers accessing from residential IP addresses, nevertheless, expertise a wholly completely different final result they’re funneled via visitors distribution techniques managed by menace actors and finally directed to malicious content material.
The Function of “Direct Search” Parking
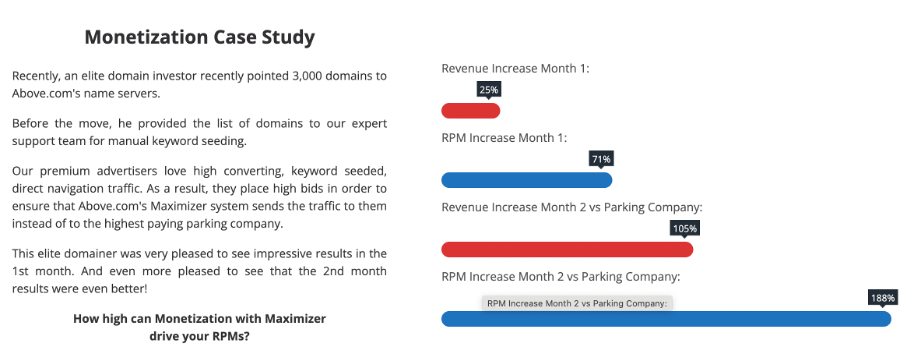
On the coronary heart of this menace ecosystem lies a monetization mannequin referred to as “direct search” or “zero-click parking.” Area house owners decide into techniques the place visitors is bought to advertisers via real-time bidding, much like legit promoting exchanges.
Customers typing a website title are redirected via a number of intermediaries every performing machine fingerprinting and profiling earlier than lastly reaching a touchdown web page.
In apply, this technique creates a worthwhile provide chain for malicious actors. A single area might move via a number of promoting networks earlier than reaching a ultimate advertiser, every layer including one other hop within the redirection chain and obscuring accountability.
The disconnect between area house owners, parking platforms, and ultimate advertisers creates exactly the form of opacity that allows crime to flourish with minimal penalties.
Analysis recognized three beforehand unreported actors working large-scale, professionally managed area portfolios concentrating on completely different demographics with hundreds of lookalike domains.
The primary actor operates practically three thousand lookalike domains via customized title servers, together with frequent typos like gmai.com.
The chatterjamtagbirdfile[.]monster website stated, “Your archive is prepared” and gave us directions to obtain the file and offered a password for the archive.
![chatterjamtagbirdfile[.]monster page leading to Tedy malware.](https://blogs.infoblox.com/wp-content/uploads/domain_parking_figure_5.png)
Past malvertising, the actor actively collects private info via electronic mail misdirection and operates enterprise electronic mail compromise campaigns distributing trojan malware.
A second actor employs refined “double quick flux” methods quickly rotating each authoritative title servers and IP addresses to evade detection.
This uncommon evasion technique, mixed with a portfolio of roughly 80,000 domains, demonstrates professional-grade operations concentrating on grownup content material, gaming platforms, and unlawful companies.
The third actor operates domaincntrol.com, a website differing by a single character from GoDaddy’s legit title servers.
By exploiting harmless typos in DNS configurations and leveraging expired domains containing outdated hyperlinks, this actor routes visitors via malicious infrastructure.
Not too long ago, this actor added focused functionality towards Cloudflare Safe DNS customers, demonstrating evolving sophistication and the power to focus on particular consumer populations selectively.
Inadvertently Gasoline the Downside
Contributing to the escalating menace, Google’s latest coverage adjustments requiring advertisers to opt-in to parking visitors inadvertently pushed area traders towards direct search parking fashions.
The preferred targets have been Netflix, Youtube, Google, Pornhub, and Newtoki, which is a platform for unauthorized distribution of manga and comics.
![A visualization of popular targets of domains that use koaladns[.]com as a name server.](https://blogs.infoblox.com/wp-content/uploads/domain_parking_figure_8.png)
As conventional promoting income declined, parking platforms actively beneficial direct search instead income supply, creating situations that will enhance consumer publicity to malicious content material.
Whereas unscrupulous advertisers ship the malicious content material, area portfolio house owners actively take part in consumer profiling and selective visitors routing, enjoying an underreported function within the menace panorama.
As direct search parking adoption accelerates, the danger to web customers continues to escalate, making even the only typo probably catastrophic.
Addressing this menace requires higher transparency all through the parking ecosystem and coordinated motion from platform operators, area registrars, and safety researchers.
Observe us on Google Information, LinkedIn, and X to Get Immediate Updates and Set GBH as a Most well-liked Supply in Google.










