In March 2024, an affiliate of the BlackCat ransomware gang took to a cybercrime discussion board with a criticism. They’d carried out the assault on Change Healthcare – one of many largest healthcare knowledge breaches in U.S. historical past – however by no means bought their lower of the $22 million ransom fee. BlackCat’s operators had taken the cash and vanished, placing up a pretend FBI seizure discover on their leak website to cowl the exit.
The grievance virtually seems like a contractor dispute. Strip away the legal factor together with the obvious double-cross, and what’s left is (hints of) one thing any firm govt would possibly acknowledge: enterprise preparations full with provide chains, pricing, competitors, and prospects who anticipate their cash’s price. In the present day’s ransomware runs on this very logic.
From the surface, nonetheless, you wouldn’t realize it. To the untrained eye, the assaults seem to be a break-in with a ransom notice hooked up – somebody will get in, locks (and steals) the vital information, leaves a crude demand, and waits for his or her rewards. Clear and easy, however virtually definitely incomplete. Understandably, the blast and particularly its affect draw the headlines, whereas every little thing that fed it stays ‘off digital camera.’ However that is solely the place the operation lastly surfaces. A lot of what made the assault attainable and profitable occurred the place nobody was wanting.
Too low-cost to fail
Behind the ransomware ‘storefront’ sits a form of franchise operation, or maybe a gig financial system, full with labor and tooling markets, subscription companies, suppliers, companions, and even one thing akin to service-level agreements between the events concerned. Collectively, they pave the best way for the intrusion lengthy earlier than the ransom notice arrives. So in case your group views a ransomware incident solely as a near-random break-in that occurred virtually as if out of nowhere, its defenses will fail to account for a way well-resourced and iterative the risk truly is.
The trade is designed so that every participant solely must be competent at their (slender) perform. The developer who maintains the ransomware platform and the model by no means has to hassle touching a sufferer’s atmosphere to earn their rewards. The affiliate pays a lower or a payment for entry utilizing credentials they didn’t harvest themselves. The preliminary entry dealer who sells a foothold into a company community doesn’t (even have to) know what the client plans to do with the logins.
However collectively, they’ve utilized the logic of the franchise to the traditional ‘artwork’ of the shakedown, splitting the load of blame alongside the best way. And each time an trade constructions itself this fashion, quantity follows.
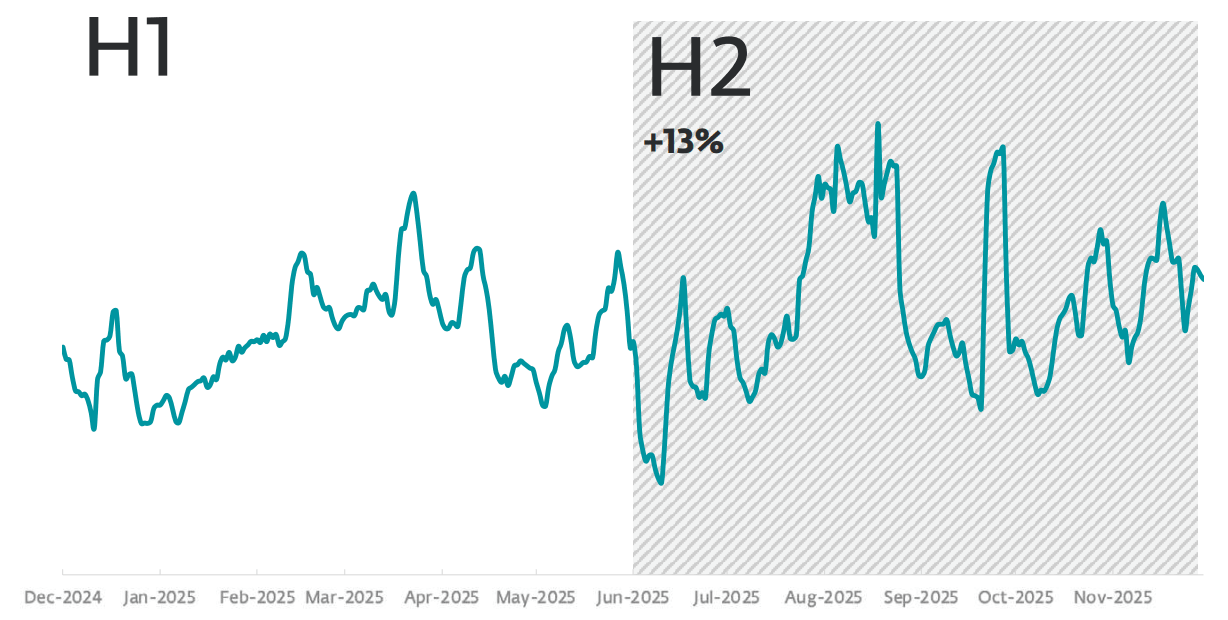
ESET’s detection knowledge reveals ransomware rising by 13 % within the second half of 2025 in comparison with the prior six months, following a 30-percent improve within the first half of 2025. In the meantime, Verizon’s 2025 Information Breach Investigations Report (DBIR) recorded a leap from 32% to 44% within the share of breaches involving ransomware, whereas the median ransom fee fell from $150,000 to $115,000. The targets are shifting, too. Mandiant’s evaluation reveals a transfer towards smaller organizations with much less mature defenses.
Extra (and softer) targets plus smaller bites equate to a textbook quantity play.
Ransomware is hardly random
Ransomware operations are constructed to scale no matter whether or not any particular person participant possesses formidable expertise. Admittedly, the internal workings of what’s typically often called ransomware-as-a-service (RaaS) are messier than these of, say, a quick meals chain – coordination is unfastened and turf wars are actual and sometimes public. Nonetheless, the underlying logic holds. The ransomware trade lives and dies by belief amongst its contributors and the incentives that bind them. And as we all know, incentives are famously recognized to find out outcomes greater than anything.
A lot in order that the sector is crowded accordingly. Competitors amongst people generally enlarges its personal type – first between people, then households, then communities, then nations. Within the digital world, particular person hackers competing for notoriety morphed into organized teams competing for territory, which grew to become an interconnected community of specialists competing for market share. Unencumbered by borders or bureaucracies, cybercriminals compressed an arc that took reliable industries many years into a few years.
Legislation enforcement doesn’t stand idly by, in fact, and focused disruptions create actual uncertainty and impose actual prices. However shutting down a agency in a aggressive market doesn’t shut down the market. Because the incentives keep aligned, the demise of a ransomware group triggers competitors amongst survivors to take its spot. New entrants emerge, others rebrand or crew up with friends, prospects select new suppliers, confirmed playbooks survive. Even the infighting amongst cybercrime teams quantities to the market purging its weaker gamers – competitors working as marketed.
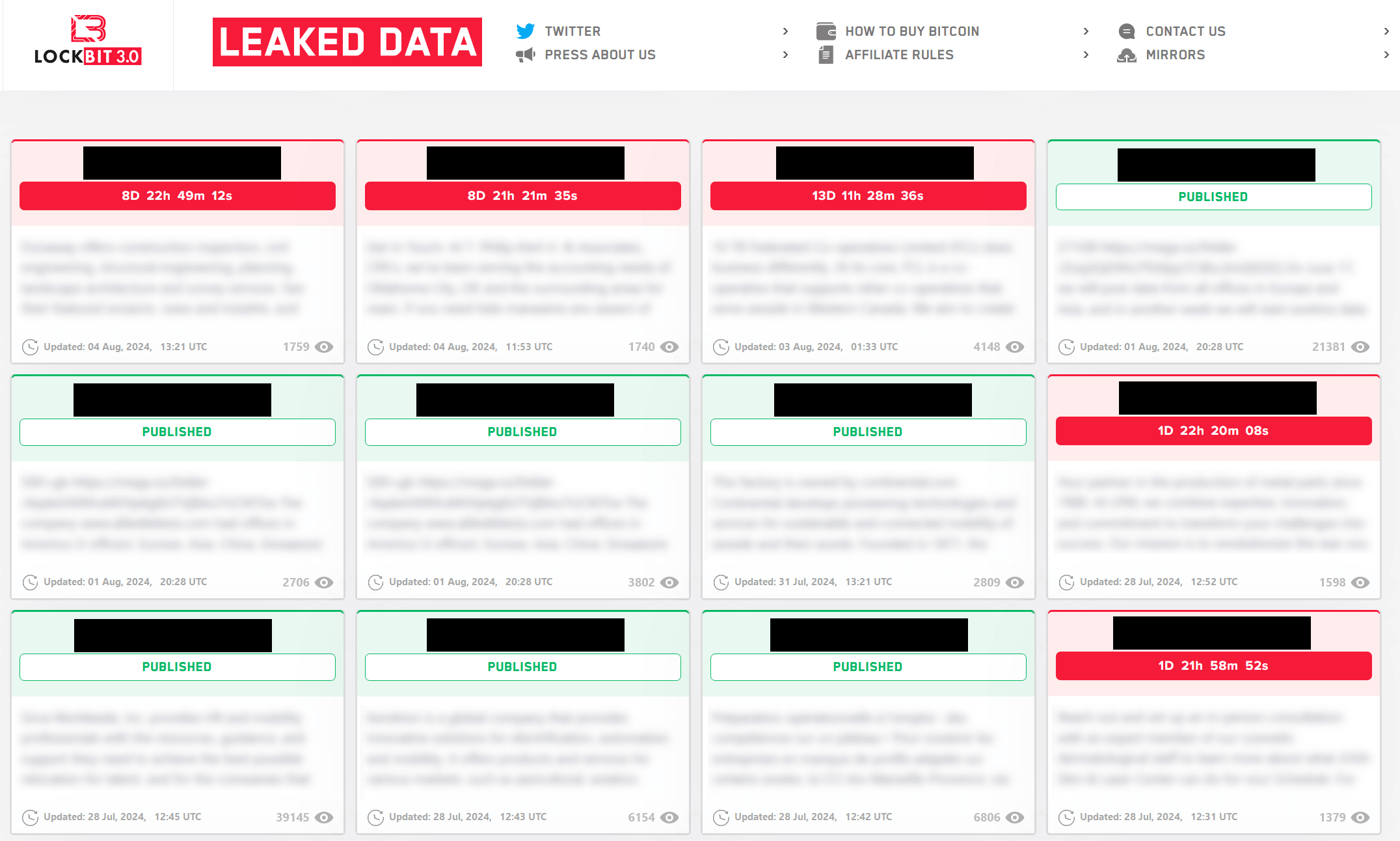
For instance, when LockBit and BlackCat had been disrupted by legislation enforcement in 2024, their associates moved primarily to RansomHub. In 2025, DragonForce – a comparatively minor participant on the time – defaced the leak websites of a number of rivals and took down the location of RansomHub, the then-leading operation. When RansomHub went quiet, Akira and Qilin absorbed its market share. The sample holds as a result of the barrier to entry stays low, the instruments can be found as a service, and the labor is so disposable that the availability can’t be starved of contributors.
The Pink Queen’s race
Through the years, the ransomware playbook of yore – lock the information and demand a ransom – has given technique to double extortion, the place attackers steal company knowledge earlier than encrypting it and publish at the very least samples from the haul on devoted leak websites. The FBI and CISA now routinely describe ransomware as a “knowledge theft and extortion” downside.
However the particular risks additionally change quick. Barely two years in the past, ClickFix – a social engineering method the place a pretend error message tips customers into copy-pasting and executing malicious instructions – was on virtually no person’s radar. Now it’s widespread and utilized by state-backed and cybercrime teams alike.
Then once more, this velocity of adaptation is hardly shocking when you notice {that a} model of it has been enjoying out in nature since, properly, without end. Species locked in competitors should repeatedly adapt merely to carry their place. Predators get sooner, so prey will get sooner. Prey develops camouflage, so predators develop sharper imaginative and prescient. Biology calls this the Pink Queen impact, named after a personality in Lewis Carroll’s By way of the Wanting-Glass who should hold operating simply to remain in place.
Safety practitioners will acknowledge the dynamic, though the extra acquainted names – similar to an arms race and a cat-and-mouse sport – could also be underselling it. The Pink Queen impact describes one thing extra particular: adaptation that produces no web benefit as a result of the opposite facet adapts virtually in parallel.
Its clearest manifestation but inhabits the house between defenders’ instruments and attackers’ anti-tools. Endpoint detection and response (and prolonged detection and response, or EDR/XDR) merchandise are key to catching the form of exercise that ransomware associates conduct inside compromised networks. Because the merchandise have improved, criminals responded by constructing a clandestine marketplace for instruments designed to disable them.
And the place there’s a market, there’s a product – usually, plenty of it.
ESET researchers observe virtually 90 EDR killers in energetic use. Fifty-four exploit the identical underlying method: loading a reliable however weak driver onto the goal machine and utilizing it to realize the kernel-level privileges wanted to close the safety product down. The method is named Carry Your Personal Weak Driver (BYOVD), and the weak drivers are a commodity – the identical driver seems throughout unrelated instruments, and the identical device migrates between drivers throughout campaigns.
The EDR killer market mirrors the ransomware financial system it serves. These anti-tools come packaged with subscription-based obfuscation companies that replace frequently to remain forward of detection. Associates, not the ransomware operators, usually select which killer to deploy – the buying determination is made on the franchise stage. When the defensive product updates, the obfuscation service follows. Pink Queen, once more.
The sheer funding in EDR killers is, considerably perversely, the clearest measure of how a lot harm the detection instruments inflict on the legal enterprise mannequin. In any case, you don’t construct a whole product class round disabling one thing that isn’t hurting your backside line.
And the anti-tools might scale additional nonetheless as AI is making the market, to not point out the broader cybercrime financial system, even simpler to hitch. ESET researchers suspect that AI assisted within the growth of some EDR killers – the wares of the Warlock gang are however one instance. The truth is, final yr ESET consultants additionally noticed the primary AI-powered ransomware, albeit not in precise assaults. Individually, different researchers have documented what they name ‘vibeware‘: AI-aided malware produced at quantity and supposed to flood the goal atmosphere with disposable code within the hopes that some will get via. The barrier to producing malware has dropped to a degree the place the constraint is intent, quite than formidable expertise – very similar to what we’ve witnessed on the broader cybercrime scene itself.
Studying the market
Viewing ransomware solely as an assault produces defenses constructed towards assaults. However take into consideration ransomware as an trade and extra priorities come into focus.
The questions price asking your self embrace: How is the Pink Queen dynamic between defensive merchandise and anti-tools evolving? Which malicious instruments, strategies and procedures are doing the rounds now? Can our safety stack keep at bay a BYOVD assault that makes use of the drivers now in circulation? What occurs to the environment if an MSP in your provide chain is compromised? Which ransomware actors are actively focusing on our sector, and which EDR killers are they shopping for?
For those who can’t reply these and different pertinent questions, it could possibly be that by the point the trade’s output reaches you, a lot of the chain has already executed. You possibly can’t predict which group will goal you, when, or via which vector. However you’ll be able to keep a present map of the place the energetic teams are going – and whether or not any of these paths may result in your door.












