For years, Mac customers have felt a sense of safety because of Apple’s strict notarization course of, a system that ensures an app’s security. Nonetheless, a brand new report from Apple gadget safety specialists at Jamf Risk Labs reveals that hackers are discovering methods to get that official seal of approval for their very own malicious instruments.
Researchers had been in a position to determine this trick whereas monitoring a software program referred to as MacSync Stealer. Prior to now, attackers relied on “clunky” methods like drag-to-terminal or ClickFix, which pressured customers to manually drag information into the Mac’s Terminal or paste coded instructions to set off an an infection. The model found now’s rather more harmful as a result of it removes these handbook steps totally.
Bypassing the Digital Guard
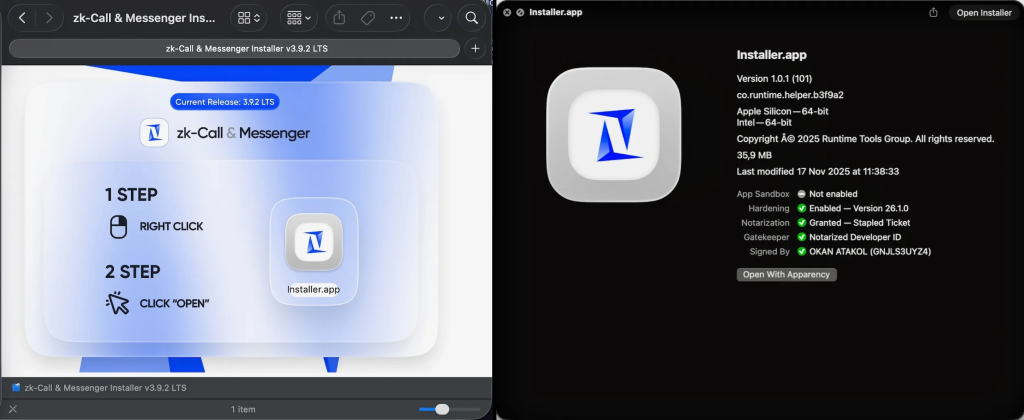
This newest model arrives disguised as a innocent installer for a chat app referred to as ‘zk-call.’ What makes this particular assault so sneaky is that it was code-signed and notarised. This implies the hackers used a fraudulent Developer Group ID (GNJLS3UYZ4) to make the Mac imagine the software program was authentic.
Based on Jamf’s weblog submit, shared with Hackread.com, the file was even ‘inflated’ with giant, ineffective PDFs to make it appear to be a heavy, skilled software.
Additional probing revealed that after you open the installer (particularly a file named zk-call-messenger-installer-3.9.2-lts.dmg), a hidden script begins working within the background. It doesn’t begin inflicting hassle straight away, although. “This shift in distribution displays a broader pattern,” the researchers famous, the place malware acts extra like a “sleeper agent” to keep away from detection.
A Affected person Thief
What’s fascinating is that MacSync Stealer is surprisingly affected person. It creates a log file at UserSyncWorker.log to trace its personal exercise. If it sees that it has already run inside the final hour (3,600 seconds), it merely goes to sleep. This ‘throttling’ makes it a lot tougher for safety software program to note a continuing, suspicious stream of knowledge.
The top purpose is a direct hit in your privateness as a result of the software program particularly hunts for the login.keychain-db. That is the grasp file the place your Mac shops each password you’ve ever saved. To get inside, it might set off a pretend pop-up asking to your system password. So, in case you see a random request to your password instantly after putting in a brand new app, it’s a large purple flag.
Apple has since revoked the digital certificates utilized by these attackers, however the incident reveals {that a} notarised app isn’t all the time a protected one.